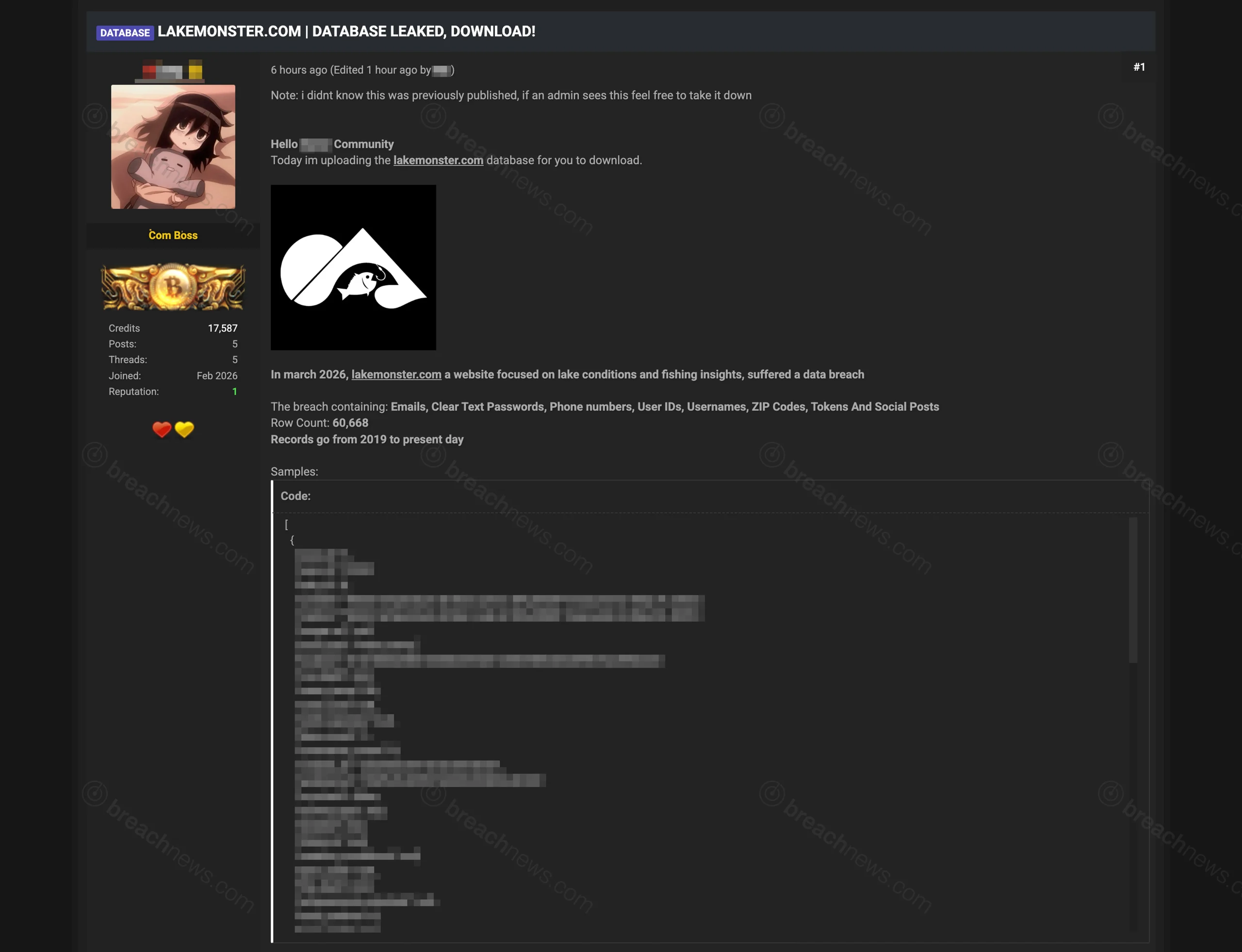
A threat actor posted what they claim is the complete database of Lakemonster.com, a fishing conditions and lake insights platform, to underground forums on March 30, 2026. The alleged dataset contains 60,668 user records spanning 2019 to present, including cleartext passwords, phone numbers, and location data.
The leaked data reportedly includes emails, usernames, phone numbers, ZIP codes, user IDs, authentication tokens, and social media posts with fishing activity logs. Sample records show detailed fishing reports with GPS coordinates, water temperature readings, catch data, and user interactions dating back multiple years.
Alleged Data Structure
The claimed breach includes fishing posts with precise location data, water temperature measurements, catch species information, and user engagement metrics. Authentication tokens and cleartext passwords would enable account takeover if the data is legitimate, while phone numbers and location history create privacy risks for outdoor enthusiasts who may have shared precise fishing locations.
Threat Actor Claims
The poster acknowledged the breach may have been previously published and offered to remove it if administrators confirmed prior disclosure. This suggests the data may have circulated privately before public release. The threat actor has one claimed breach according to tracking data, with no established reputation in breach communities.
Lake Monster has not issued a public statement regarding the alleged incident. The platform provides lake conditions, fishing reports, and community features for anglers tracking water temperatures, ice conditions, and catch activity across US lakes.
Independent Verification
BreachNews has not independently verified the authenticity of the claimed data or confirmed any security incident at Lake Monster. Users concerned about potential exposure should change passwords, enable multi-factor authentication if available, and monitor accounts for unauthorized activity.