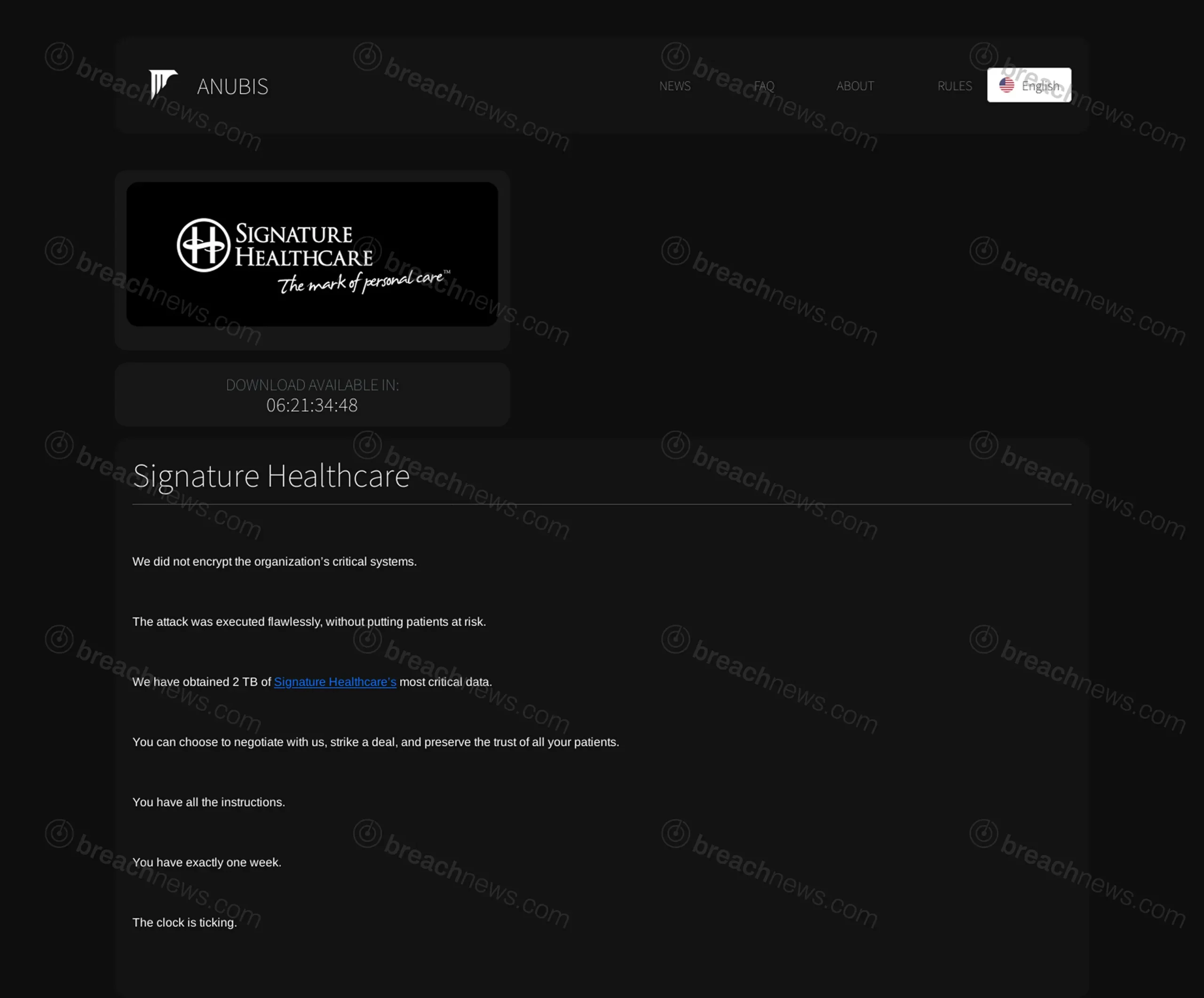
Anubis ransomware has claimed responsibility for the cyberattack on Signature Healthcare, the Massachusetts-based health system that has been operating under downtime procedures since April 6, 2026. The group alleges it exfiltrated 2 TB of data from the organization and has issued a one-week deadline for Signature Healthcare to begin negotiations before it publishes the stolen files.
What Happened at Brockton Hospital
Signature Healthcare detected the cyberattack on April 6 and immediately activated downtime procedures across its information systems. Brockton Hospital, the health system’s 216-bed community teaching hospital in Brockton, Massachusetts, diverted ambulances to alternate facilities and canceled chemotherapy infusion treatments for cancer patients. Its electronic medical record system and patient portal were taken offline. Emergency services and walk-in care remained operational, with staff relying on manual processes throughout the disruption.
The health system serves more than 70,000 patients annually across Southeastern Massachusetts through Brockton Hospital and 15 outpatient care locations operated by Signature Medical Group. It is affiliated with Beth Israel Deaconess Medical Center. In a statement, Chief Operating Officer Kim Walsh said the organization was working with third-party cybersecurity experts and state and federal officials to investigate the incident, adding that care teams were continuing to provide services under downtime procedures.
Signature Healthcare has not confirmed a ransomware attack or attributed the incident to any specific group. The organization had not issued any update on the Anubis claim at time of publication.
Anubis Claims Data Theft, Not Encryption
Anubis posted Signature Healthcare to its extortion site today, claiming to have obtained 2 TB of the health system’s most critical data. The group stated it did not encrypt Signature Healthcare’s clinical systems, framing the decision as a deliberate choice to avoid putting patients at risk. The posting included a countdown timer with approximately six days remaining — placing the deadline around April 15 — and directed the organization to contact the group using instructions already provided.
The group’s claim that it avoided encrypting clinical systems out of concern for patient safety warrants scrutiny. Extortion groups increasingly use this framing as a calculated positioning move rather than evidence of restraint. By skipping encryption, Anubis avoids triggering the kind of immediate operational paralysis that draws law enforcement attention and public outrage, while still maintaining full leverage through the threat of a data release. The absence of encryption does not reduce the severity of a potential 2 TB data exposure for patients whose protected health information may be included.
This approach is consistent with Anubis’s documented methodology. The group operates a data theft and extortion model rather than deploying file-encrypting ransomware, using the threat of public data release as its primary leverage. BreachNews has previously covered Anubis’s claim against Publishers Clearing House using the same playbook.
The Stakes for Patients
A 2 TB exfiltration from a regional health system of this size would likely encompass a substantial volume of protected health information, including patient records, billing data, insurance details, and clinical documentation. The cancellation of chemotherapy infusions during the disruption illustrates that even data-theft-only attacks against healthcare organizations carry direct patient safety consequences when systems are taken offline during the investigation.
Under HIPAA’s Breach Notification Rule, covered entities are required to notify affected individuals within 60 days of discovering a breach involving unsecured protected health information. If the Anubis claim is substantiated and patient data was exfiltrated, Signature Healthcare would be obligated to notify impacted patients, report the breach to the Department of Health and Human Services, and, given the likely scale, notify prominent media outlets in affected states. The clock on that 60-day window began when the incident was detected on April 6.
Signature Healthcare had not issued any public statement on the Anubis claim at time of publication. Patients of Signature Healthcare or Brockton Hospital with concerns about their information can review the guidance in our data breach response guide.