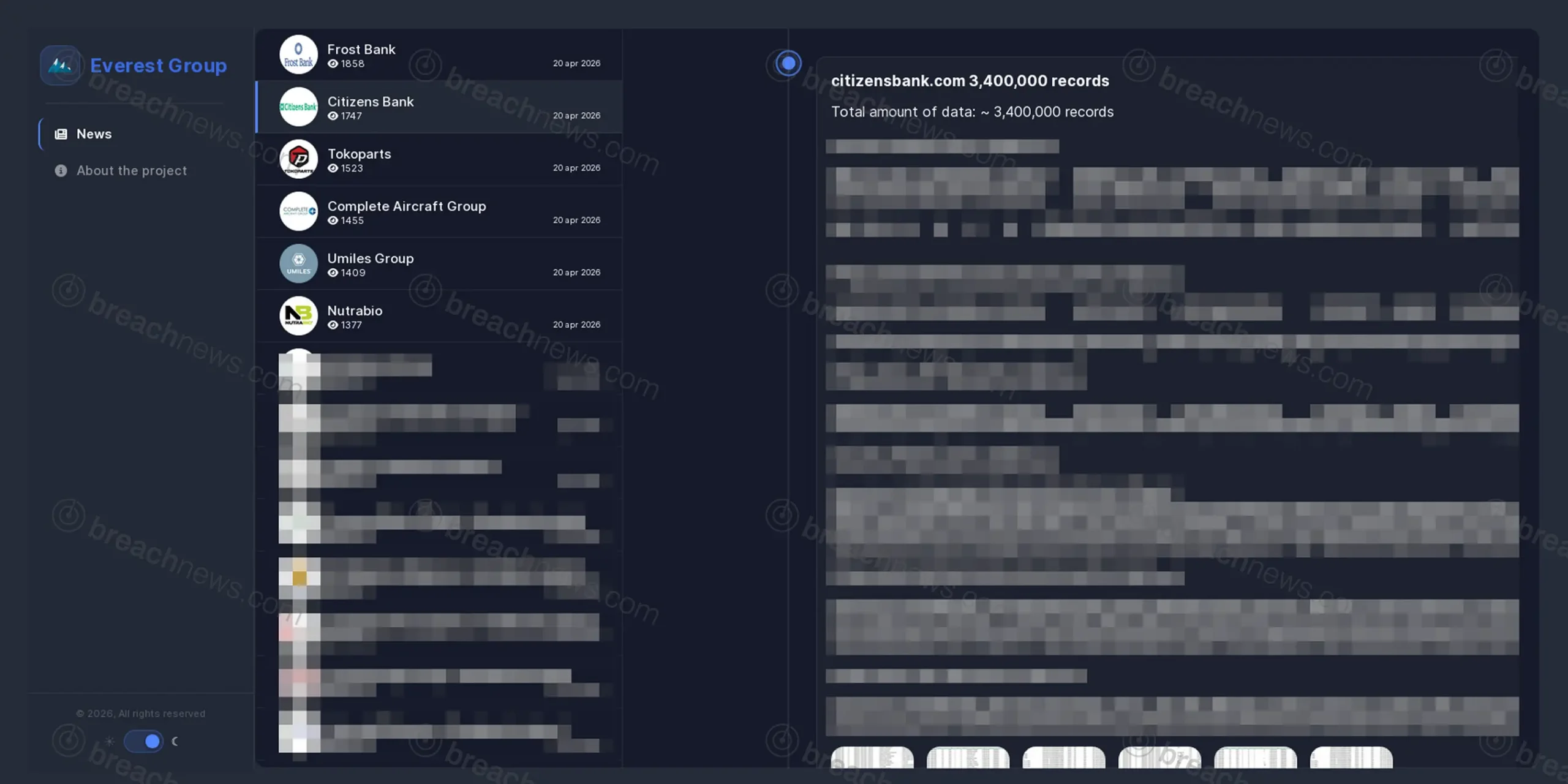
The Everest extortion group listed Citizens Bank on its dark web leak site on April 20, 2026, claiming to have exfiltrated 3.4 million records from the Providence, Rhode Island-based financial institution and threatening public release via a countdown timer. The posting is part of a broader wave the group made within the same 24-hour window, simultaneously listing Frost Bank and organizations across aviation, automotive, and retail sectors.
What the Leak Page Shows
The group’s listing for Citizens Bank specifically claims 3.4 million records and includes data samples drawn from what appears to be a document processing and statement production system. The sampled files reference internal job processing tables, customer account numbers, customer names, and mailing addresses associated with Citizens Bank deposit account statements across multiple states. File paths in the samples point to a system identified as HARMONIE_PRODUCER, containing tables for document tracking, statement processing, and mailing workflows — with jobs organized by bank branch codes covering Pennsylvania, New York, and Massachusetts operations.
The nature of the exposed data suggests the breach may involve a third-party document production or print-and-mail vendor rather than Citizens Bank’s core banking infrastructure directly. If accurate, it would represent a supply chain compromise rather than a direct intrusion into the bank’s own network. That distinction has not been confirmed, and Citizens Bank had not issued any public statement at time of publication.
A live countdown timer on the listing indicates the group intends to publish the full dataset when it expires.
Everest’s Operational Model
Despite the ransomware label, Everest does not reliably deploy file encryption. The group, active since December 2020 and assessed by researchers as Russian-speaking and financially motivated, operates primarily as a data theft and extortion operation. It exfiltrates sensitive data, lists victims on its leak site with countdown timers, and publishes or sells stolen material when negotiations collapse. The group has also functioned as an initial access broker, selling footholds in compromised networks to other threat actors.
Everest gains initial access primarily through compromised remote desktop credentials, purchased access from brokers, and — since October 2023 — a documented insider recruitment program targeting employees at US, Canadian, and European organizations. Once inside, the group uses tools including Cobalt Strike for command and control, ProcDump against LSASS for credential harvesting, and WinRAR for staging exfiltrated data before moving it out of the network. A defining operational characteristic is systematic deletion of all tools after each execution stage to hinder forensic investigation.
The group’s recent track record includes a September 2025 claim against Collins Aerospace that disrupted check-in and baggage systems at Heathrow, Brussels, and Berlin airports. Everest’s own leak site was defaced in April 2025 — an action security researchers have tentatively attributed to rival group DragonForce — but operations recovered by mid-2025 and the group has maintained a consistent posting tempo since.
The Target
Citizens Bank is a subsidiary of Citizens Financial Group, one of the largest retail and commercial banks in the United States. The bank operates branches across the northeastern and midwestern US and offers a full range of consumer and business banking products including checking and savings accounts, mortgages, credit cards, and wealth management services. A breach involving customer statement and account data at an institution of this scale would carry significant regulatory exposure under the Gramm-Leach-Bliley Act and applicable state financial privacy laws.
If you have received a data breach notification, visit our guide on how to respond.