Vercel has confirmed unauthorized access to certain internal systems in a security incident disclosed April 19, 2026. The company has engaged incident response experts, notified law enforcement, and begun contacting a limited subset of customers it has identified as impacted. ShinyHunters has separately claimed responsibility, alleging theft of internal access keys, source code, employee accounts, API keys, NPM tokens, GitHub tokens, and data from Vercel’s internal Linear project management system and user management systems — listing the alleged dataset for $2 million. Vercel has not confirmed the scope or attribution of the breach beyond its own advisory.
What vercel has confirmed about the incident
Vercel’s security bulletin, updated April 19, states the company identified a security incident involving unauthorized access to certain internal systems. The company said it has engaged incident response specialists to assist with investigation and remediation, and has notified law enforcement. Vercel confirmed it has identified a limited subset of customers that were impacted and is engaging with them directly. The company said its services remain operational and committed to updating its advisory as the investigation progresses.
Critically, Vercel is recommending that all customers — not just confirmed victims — review their environment variables and take advantage of Vercel’s sensitive environment variable feature, which restricts decryption of secret values to build time only. Security researchers with knowledge of the incident have indicated that environment variables marked as sensitive appear to have been protected, but non-sensitive environment variables should be treated as potentially exposed and rotated as a precaution. Any Vercel customer storing API keys, database credentials, third-party service tokens, or other secrets in non-sensitive environment variables should treat rotation as an immediate priority.
We’ve identified a security incident that involved unauthorized access to certain internal Vercel systems, impacting a limited subset of customers. Please see our security bulletin:https://t.co/0S939n3qHC
— Vercel (@vercel) April 19, 2026
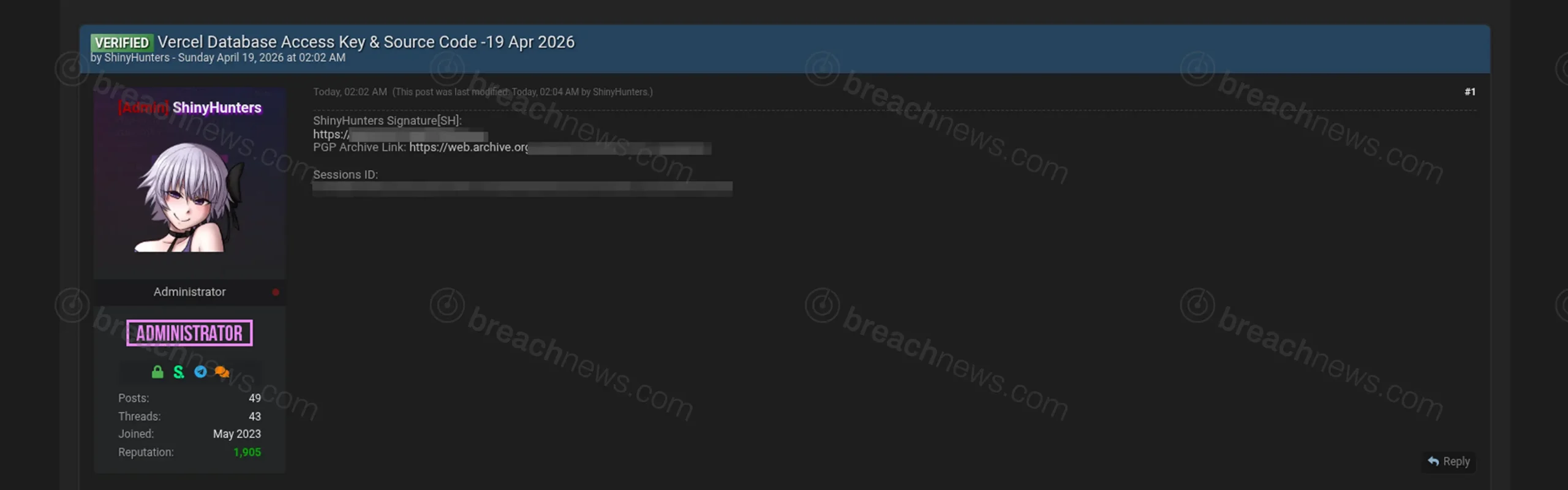
Shinyhunters claims access to internal systems and tokens
A post attributed to ShinyHunters is offering alleged Vercel internal data for $2 million. The claimed dataset includes access keys, source code, employee account data, API keys, NPM tokens, GitHub tokens, and records from Vercel’s internal Linear issue tracker and user management systems. The group has previously listed and published data from a series of supply chain and SaaS-linked intrusions in 2026, including confirmed breaches at Rockstar Games, McGraw Hill and Kemper, and the European Commission. ShinyHunters’ attribution has not been independently verified by Vercel or law enforcement at time of publication.
Why environment variables are the real risk here
Vercel is among the most widely used deployment platforms in the industry, serving millions of developers and powering production infrastructure for companies ranging from early-stage startups to major enterprises. The platform hosts Next.js deployments, serverless functions, and CI/CD pipelines, with environment variables routinely used to store some of the most sensitive secrets in a company’s stack — database connection strings, third-party API keys, payment processor credentials, authentication secrets, and cloud provider tokens.
If environment variable data was accessed at scale, the downstream exposure across Vercel’s customer base could be significant. A single compromised API key or cloud credential can provide an attacker persistent access to infrastructure entirely separate from Vercel itself. The incident also fits squarely into ShinyHunters’ 2026 campaign pattern: targeting developer tooling, SaaS integrations, and cloud-adjacent platforms where a single point of access yields leverage across hundreds or thousands of downstream organizations. For background on ShinyHunters’ documented operations and tactics, see the ShinyHunters threat actor profile.
Vercel customers should rotate all non-sensitive environment variables immediately, audit connected integrations including GitHub, NPM, and any third-party services, and monitor Vercel’s advisory page for updates as the investigation continues.