Update (May 8, 2026): Several organizations named in ShinyHunters’ April 2026 coordinated extortion campaign now have varying levels of confirmation, ranging from verified breach listings to company investigations and unverified claims.
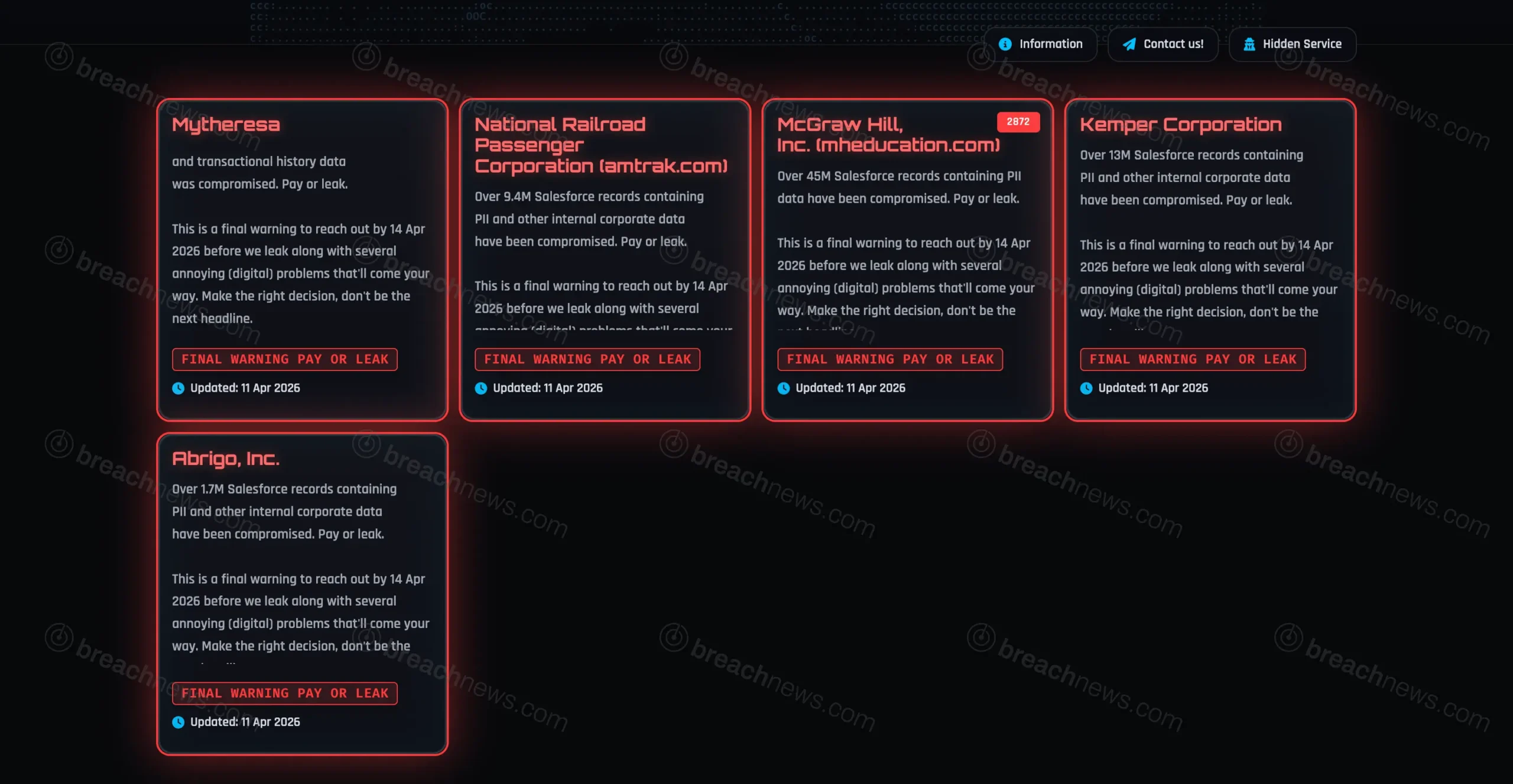
- Amtrak: Data attributed to Amtrak has been cataloged by breach notification services, with exposed information including email addresses, names, physical addresses, and support tickets. No public acknowledgment from the company has been issued at time of publication.
- McGraw Hill: The company acknowledged unauthorized access to a limited dataset tied to a Salesforce-hosted webpage. Exposed data includes email addresses, names, phone numbers, and physical addresses.
- Kemper Corporation: The company confirmed it is investigating a cybersecurity incident following the claims. However, specific exposed data fields have not been publicly confirmed.
- Mytheresa: Reported as part of the campaign, but no company acknowledgment or independently verified dataset has been confirmed.
- Abrigo: Claimed by ShinyHunters as a source of Salesforce data, but no public confirmation or independent validation has been identified.
The differing levels of validation reflect a broader pattern in ShinyHunters operations, where some incidents are substantiated through external analysis or company disclosures, while others remain based solely on threat actor claims. Several of the validated datasets have been cataloged by Have I Been Pwned.
The ShinyHunters threat group has listed multiple organizations in what appears to be a coordinated extortion campaign, alleging breaches affecting companies including Amtrak, McGraw Hill, Kemper, Mytheresa, and Abrigo.
The listings follow the group’s established “pay-or-leak” model, where organizations are publicly named alongside claims of stolen data and given a deadline to negotiate before the information is released.
Amtrak, McGraw Hill, and Kemper listed in coordinated campaign
The campaign involves multiple organizations posted within a short timeframe, suggesting a structured operation rather than isolated breach events. Each listing includes brief descriptions of the alleged data and references to internal systems or datasets, though supporting technical evidence is limited.
The lack of detailed proof across listings makes it difficult to independently verify the scope or authenticity of each claim at the time they were first published.
Extortion deadlines and data leak threats issued across listings
ShinyHunters applied consistent pressure tactics across the campaign, issuing deadlines and warning that data would be publicly released if negotiations failed. This approach mirrors previous incidents where the group followed through on threats after deadlines expired.
Rather than focusing on system disruption, the campaign centers on data exposure and reputational impact, reinforcing the group’s data-first extortion model.
Limited detail across listings complicates verification
Across the campaign, the group provided minimal technical detail, with no comprehensive datasets or verifiable samples included in several listings. This uneven level of evidence complicates efforts to distinguish between confirmed breaches and unverified claims.
Some listings referenced large volumes of data or access to internal systems, but without independent validation, these claims remain difficult to assess.
Structure mirrors recent ShinyHunters multi-company operations
The campaign aligns with a broader pattern of activity in which ShinyHunters lists multiple organizations simultaneously, combining breach claims with coordinated messaging and deadline-driven pressure.
BreachNews has previously reported on similar multi-company campaigns involving retail, financial, and technology organizations, often tied to cloud-based data exposure or third-party access points.
No public statements from listed organizations at time of initial reporting
At the time the campaign was first observed, none of the listed organizations had issued public statements addressing the claims. As with similar incidents, confirmation and impact details have emerged unevenly over time.
The combination of verified breaches, ongoing investigations, and unconfirmed claims highlights the complexity of assessing large-scale extortion campaigns as they develop.