Update (May 28, 2026): Several organizations named in the ShinyHunters campaign now have varying levels of confirmation, ranging from verified breach listings to unverified claims.
- Zara / Inditex: Inditex acknowledged unauthorized access to transaction databases hosted by a former third-party provider. Analysis indicates exposed data includes email addresses, geographic locations, purchase information, and support records. The company stated that passwords and payment data were not affected.
- Pitney Bowes: The company acknowledged unauthorized access to records within its Salesforce environment following a phishing incident involving an employee account. Reported data exposure includes email addresses, names, phone numbers, physical addresses, and job titles.
- Carnival Corporation: Carnival has since confirmed that attackers copied personal information belonging to approximately 5.9 million individuals following a phishing and social engineering incident involving a compromised employee account. Reported exposed data includes names, email addresses, dates of birth, loyalty membership information, and internal customer identifiers.
- 7-Eleven: Reported to be part of the campaign, but no company acknowledgment or independently verified dataset has been confirmed. The claim remains unverified.
- Canada Life: The company disclosed a 2026 extortion-related breach linked to the ShinyHunters group that exposed personal information belonging to some customers, including names, email addresses, phone numbers, physical addresses, and limited support-related data.
- Mytheresa: Reported as a potential victim, but no company acknowledgment or independently verified dataset has been confirmed. The claim remains unverified.
The differing levels of validation reflect a broader pattern in ShinyHunters operations, where some incidents are substantiated through external analysis or company disclosures, while others remain based solely on threat actor claims. Several of the validated datasets have been cataloged by Have I Been Pwned.
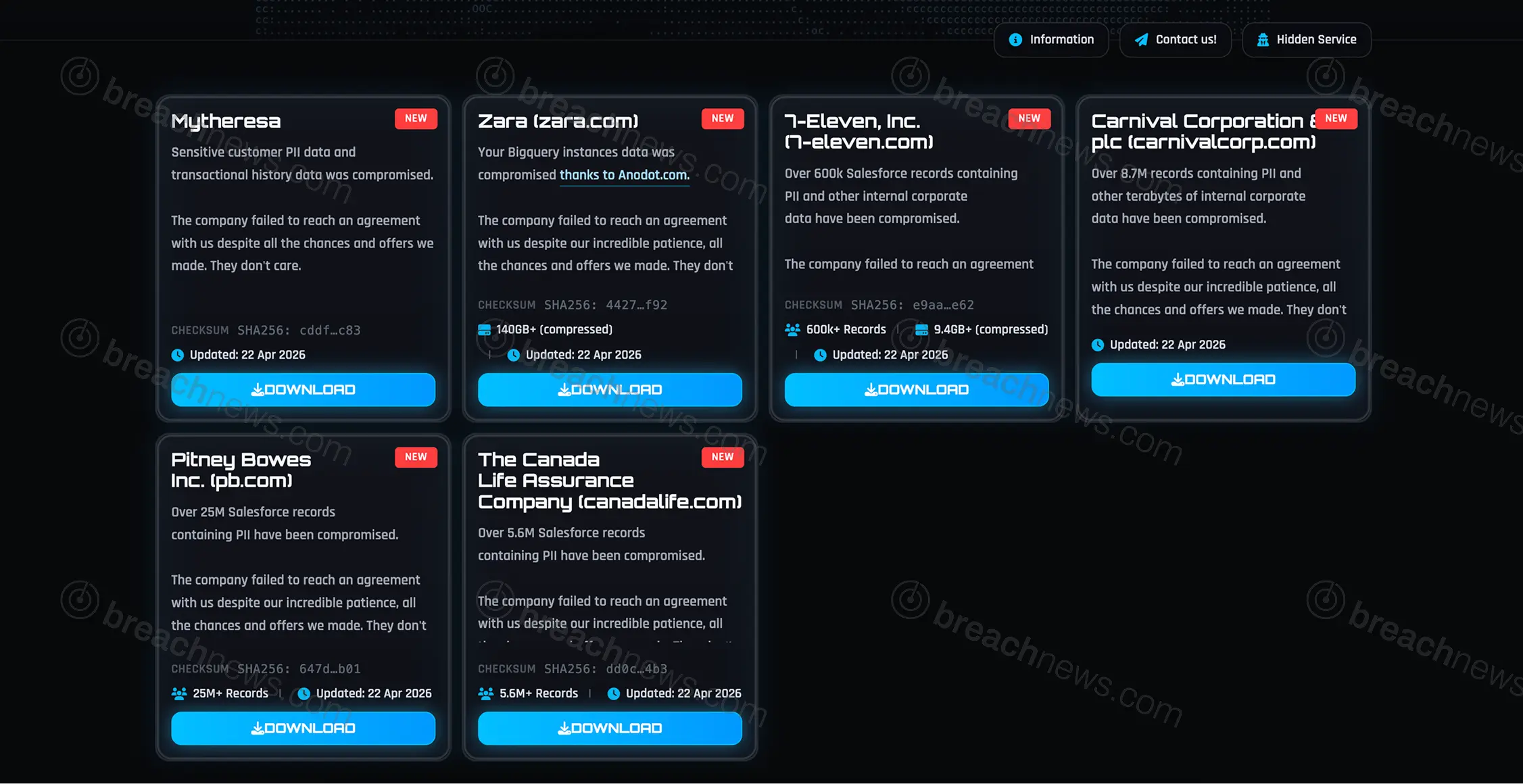
The threat actor group ShinyHunters has allegedly released data tied to multiple organizations, including Carnival Corporation, Zara, 7-Eleven, Pitney Bowes, and others, marking a significant escalation in an ongoing extortion campaign linked to large-scale data theft operations. The latest post follows earlier breach claims and appears to represent a shift from listing victims to actively publishing datasets.
Multiple organizations added to expanding victim list
According to the group’s latest update, the affected organizations include Mytheresa, Zara, 7-Eleven, Carnival Corporation & plc, Pitney Bowes, and The Canada Life Assurance Company. Each listing is accompanied by claims that negotiations failed, prompting the release of allegedly stolen data.
The datasets are described as containing a mix of personally identifiable information, transactional records, and internal corporate data. In several cases, ShinyHunters specifically referenced Salesforce-related records, continuing a pattern observed across earlier campaigns tied to misconfigured cloud environments.
Salesforce data exposure pattern continues across new listings
Several of the newly listed organizations are associated with claims of compromised Salesforce environments. The actor alleges access to large volumes of records, including more than 25 million entries in one case and over 600,000 records in another. These datasets are described as containing customer information alongside internal business data.
The repeated reference to Salesforce aligns with a broader campaign that has been active since late 2025, in which threat actors have targeted misconfigured cloud environments to extract data at scale. Previous incidents attributed to ShinyHunters have similarly involved Salesforce datasets, often tied to guest access misconfigurations or exposed data interfaces.
In the case of Zara, the group attributed access to a third-party platform, though no technical evidence has been provided to support the claim or clarify the role of external systems in the alleged breach.
Scale of claims continues to outpace verification
ShinyHunters has claimed responsibility for breaching a large number of organizations in recent weeks, though the accuracy and scope of those claims remain unclear. The group frequently lists multiple victims in rapid succession, often without providing technical details or verifiable proof of access.
A previous wave of listings covered by BreachNews included Amtrak, McGraw Hill, and Kemper Corporation, several of which were later followed by alleged data releases after deadlines passed. In at least some cases, datasets were published despite ongoing investigations or disputes over the scope of the breach.
At this stage, none of the newly listed organizations have publicly confirmed the alleged breaches or data releases. As with earlier claims, verification remains limited to threat actor statements, and it is not yet known whether the datasets described are authentic, complete, or previously undisclosed.
Ongoing investigation and potential downstream risk
If the claims are accurate, the exposure of large volumes of customer and corporate data could introduce long-term risks, including targeted phishing campaigns, identity fraud, and follow-on attacks against affected organizations. Data tied to CRM systems is often structured and detailed, increasing its value in social engineering scenarios.
For a broader overview of the group’s activity and history, see the BreachNews profile on ShinyHunters.
Further developments are likely as affected organizations investigate the claims or as additional datasets are analyzed and verified.