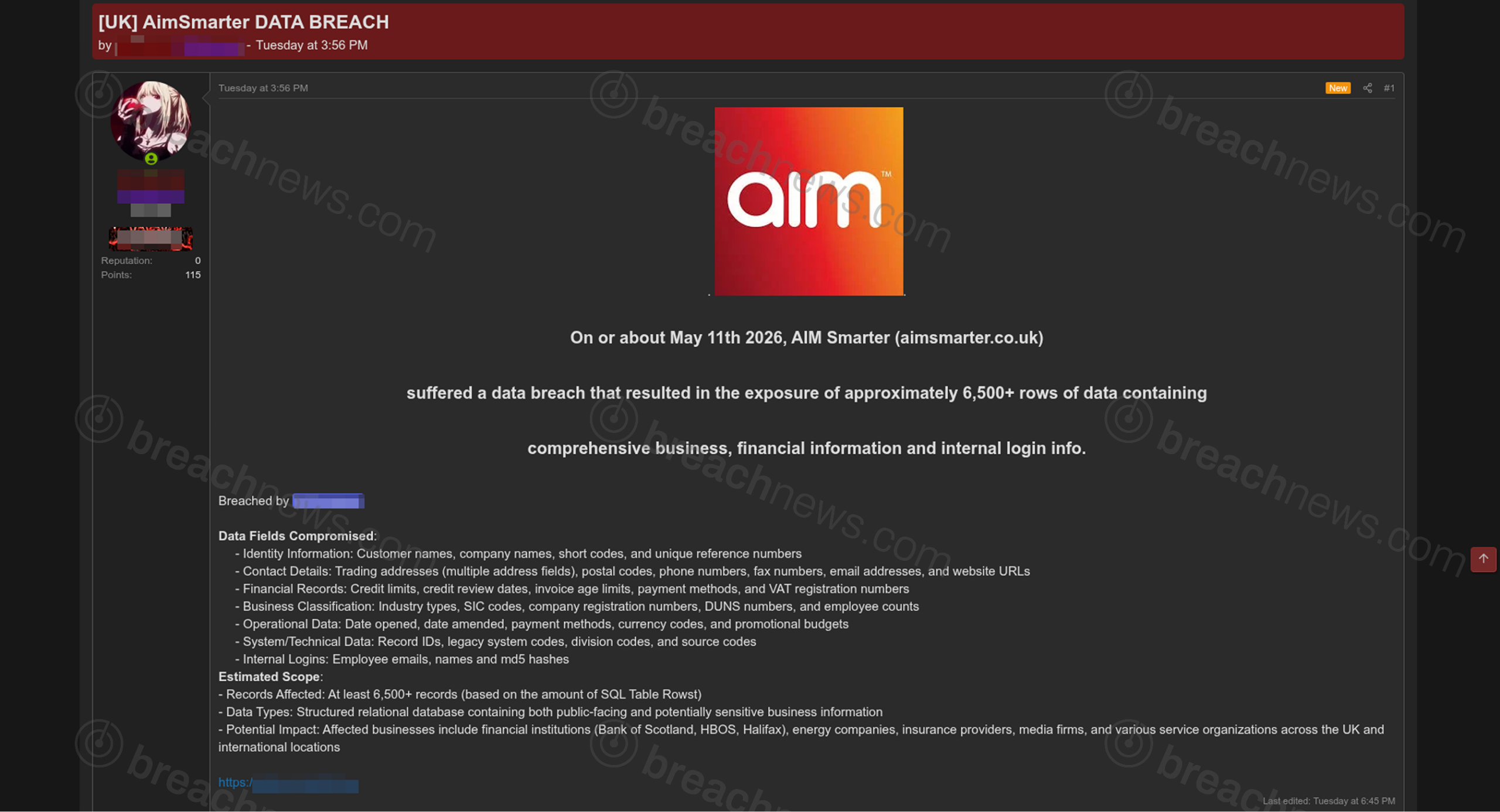
A threat actor has claimed responsibility for an alleged data breach involving UK-based technology firm AimSmarter, stating that thousands of business and internal records were exposed in the incident.
According to the forum post, the alleged breach occurred on or around May 11, 2026, and reportedly exposed approximately 6,500 rows of structured database records tied to customers, businesses, and internal systems.
The leaked data allegedly includes customer names, company information, addresses, phone numbers, email addresses, VAT registration numbers, payment methods, credit limits, invoice-related data, and internal business classification records.
The actor also claims the dataset contains employee login information, including email addresses and MD5 password hashes tied to internal accounts.
BreachNews was unable to independently verify the authenticity of the full dataset at time of publication.
Financial and operational business records allegedly exposed
The forum post describes the leaked database as containing a mixture of operational, financial, and administrative business records.
Allegedly exposed information includes industry classifications, company registration numbers, DUNS identifiers, employee counts, promotional budgets, payment terms, and internal reference codes.
The threat actor further claimed that the records reference organizations operating across financial services, insurance, energy, media, and other UK business sectors.
Although much of the exposed information appears business-related rather than consumer-focused, the presence of financial records and employee authentication data could still present downstream security risks if authentic.
Weak or reused password hashes may potentially expose internal systems or connected accounts to credential stuffing attacks, particularly if employees reused passwords across services. Similar compromises involving exposed internal credentials have increasingly overlapped with broader credential theft and infostealer activity.
Actor has limited public track record
The threat actor behind the claim does not appear to have an extensive or well-established public breach history compared to larger ransomware or extortion operations.
Recent activity tied to the same account includes several alleged database leaks and access sales involving organizations across multiple countries and industries, though the credibility of those claims remains difficult to independently assess.
The alleged AimSmarter breach was posted publicly alongside a downloadable archive reportedly containing the exposed data.
At time of publication, AimSmarter had not issued any public statement regarding the alleged incident.
The incident highlights the continuing risks posed by publicly leaked business databases, particularly when operational records and employee authentication data are exposed together.