Update April 26, 2026: ADT has confirmed a cybersecurity incident involving unauthorized access to its systems, stating that a limited set of customer and prospective customer data was accessed. The company said it contained the activity and is working with third-party cybersecurity experts and law enforcement. ADT has not confirmed the scale of the breach or the 10 million records claimed by ShinyHunters.
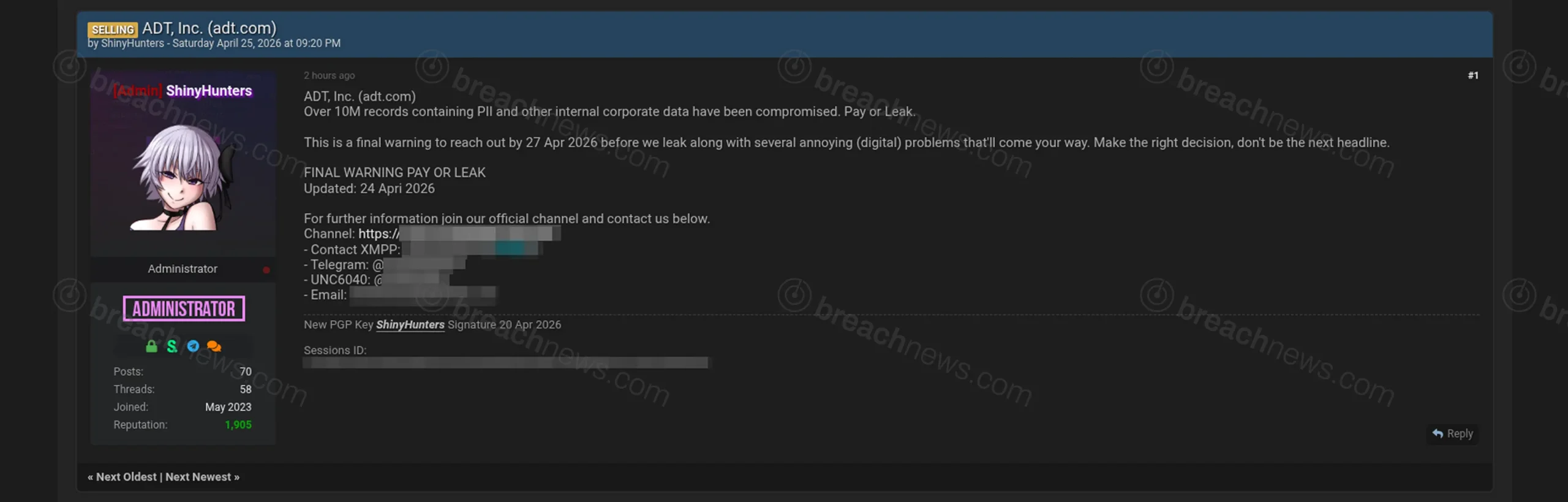
ShinyHunters is claiming a data breach involving ADT, Inc., alleging the theft of more than 10 million records containing personally identifiable information and internal corporate data. The claim surfaced April 25, 2026, accompanied by a deadline-backed extortion demand warning of a potential data leak if negotiations are not initiated.
Threat actor issues deadline-backed extortion demand
According to the listing, the group has issued what it describes as a final warning, giving ADT until April 27, 2026 to respond before the data is allegedly released. The post includes language commonly associated with extortion campaigns, warning of additional “digital problems” if demands are not met.
No technical evidence, system details, or independently verifiable material has been provided to support the claim, making it difficult to assess the authenticity or scope of the alleged breach.
Scope of alleged data exposure remains unclear
ShinyHunters claims the dataset includes more than 10 million records containing personally identifiable information alongside internal corporate data. However, the specific data types involved have not been disclosed, and it remains unclear whether the records relate to customers, employees, or other entities.
No details have been provided regarding the method of access or which systems may have been affected, leaving key questions about the nature of the alleged compromise unanswered.
Security provider status raises potential impact concerns
As a provider of alarm systems, monitoring services, and security infrastructure for residential and commercial customers, ADT operates systems tied to physical security and emergency response workflows. Any confirmed compromise involving customer or internal data could introduce additional risks beyond standard data exposure, depending on the nature of the systems involved.
Security service providers are often considered high-value targets due to the sensitivity of the data they manage and their role in protecting physical environments. Even limited exposure may carry downstream implications depending on how the data is used.
Deadline-driven extortion follows established ShinyHunters playbook
The use of time-limited demands and pay-or-leak messaging aligns with patterns observed across recent ShinyHunters activity. Recent reporting by BreachNews documented a wave of alleged data releases impacting multiple organizations after failed negotiations, including Zara, 7-Eleven, and Carnival Corporation.
This approach mirrors other campaigns where data is allegedly released after deadlines pass or negotiations break down. Previous incidents involving financial sector organizations have shown similar escalation patterns tied to extortion timelines.
A broader overview of the group’s activity is available in the ShinyHunters threat actor profile.
Confirmed incident, scale remains disputed
ADT has confirmed a cybersecurity incident involving unauthorized access to its systems and stated that a limited set of customer and prospective customer data was accessed. However, the company has not confirmed the scale of the breach or the 10 million records claimed by ShinyHunters.
As with similar listings, the claims remain unverified and are based solely on threat actor statements. Further developments may emerge if data is released or independently analyzed following the stated deadline.
This article has been updated to reflect new information provided by ADT.