The fallout from the Instructure Canvas data breach continues to expand, with multiple U.S. schools, universities, and statewide education systems now reporting potential exposure of student and staff data linked to the incident.
What began as a company-level disclosure has rapidly evolved into a broader education sector issue, as institutions across several states confirm they are investigating impact tied to the widely used Canvas learning management system.
At time of publication, the full scope of affected organizations remains unclear, though recent disclosures suggest the number of impacted institutions may be significantly higher than initially understood.
Universities and school systems report potential exposure
Major institutions have begun publicly acknowledging possible involvement in the breach. The University of Pennsylvania confirmed it is investigating the incident following reports of unauthorized access tied to Canvas. Similarly, the University of Wisconsin system reported that multiple campuses may have been affected.
At the K-12 level, school districts in North Carolina, Virginia, and California have also disclosed potential exposure. In North Carolina, officials indicated that data tied to a statewide Canvas deployment may have been accessed, potentially affecting students and staff across public schools.
Additional reporting from California suggests multiple districts are assessing impact, while a Virginia district stated that early findings indicate limited exposure, though investigations remain ongoing.
Leaked school list suggests broader impact
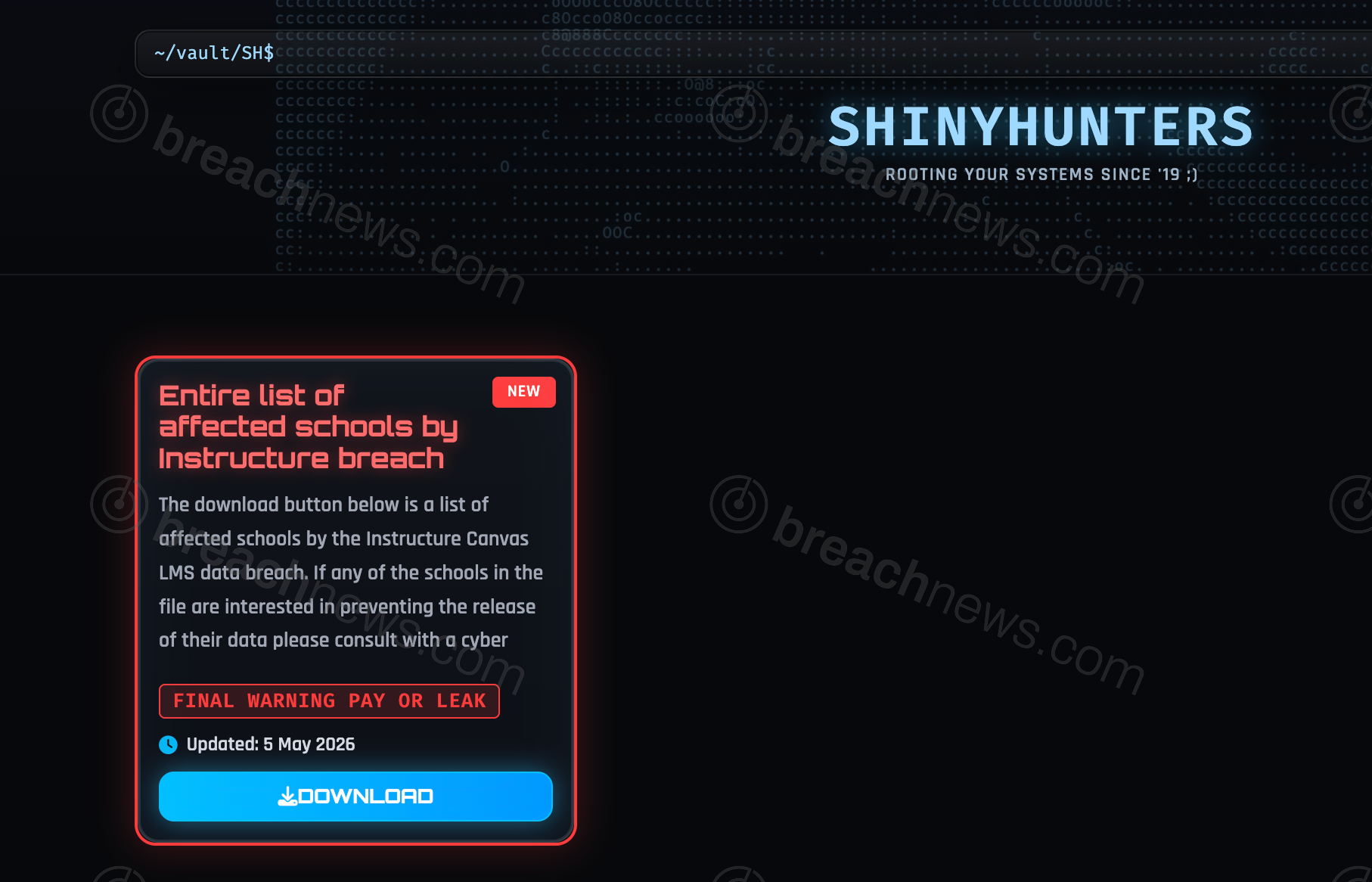
The expanding list of affected institutions aligns with earlier developments in the breach, where ShinyHunters released a dataset allegedly identifying impacted schools using the Canvas platform.
That list, which includes a large number of educational institutions, suggests the breach may extend far beyond the initial disclosures. While not independently verified, the dataset has become a reference point for organizations assessing potential exposure.
The presence of both higher education institutions and K-12 systems on the list indicates the incident may affect a wide cross-section of the education sector.
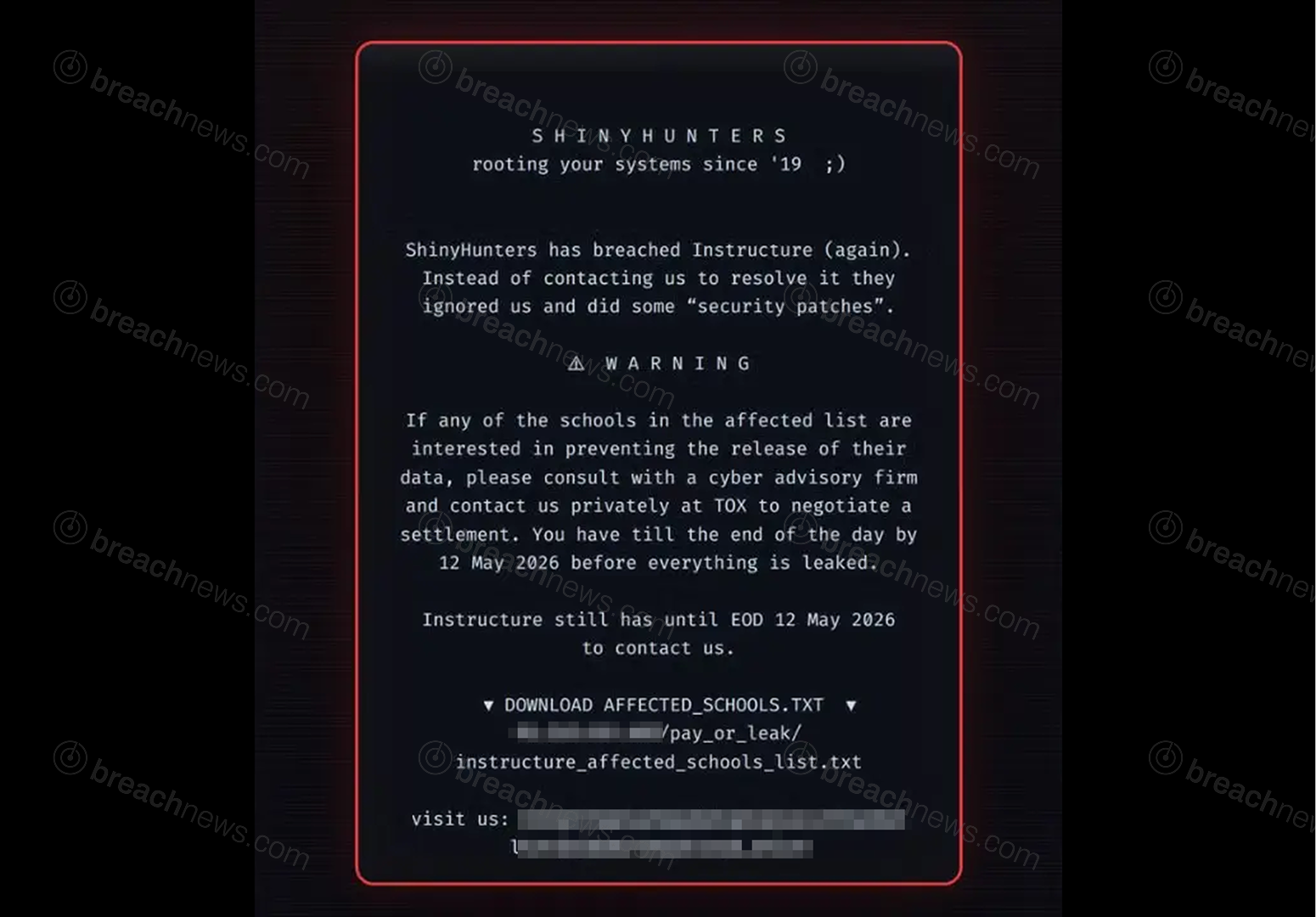
Coordinated messaging points to structured extortion effort
Material associated with the campaign shows a consistent message directed at affected institutions, warning that data may be released unless negotiations take place. The message references a deadline and instructs impacted organizations to engage privately to prevent publication.
This approach aligns with known ShinyHunters tactics, where public pressure and deadline-driven messaging are used to accelerate engagement and increase the likelihood of payment.
The inclusion of a downloadable list of schools further suggests an attempt to broaden pressure beyond the primary target, potentially involving multiple institutions in the extortion process.
Incident remains under investigation
Instructure has confirmed that unauthorized access occurred and that user data, including names, email addresses, and communications, may have been exposed. However, the company has not disclosed a full list of affected institutions or clarified the total number of impacted individuals.
The growing number of organizations reporting involvement highlights the complexity of the incident, particularly given Canvas’ role as a shared platform used across thousands of educational environments.
Security experts note that centralized platforms like learning management systems create unique risk profiles, where a single compromise can have cascading effects across multiple independent organizations.
As investigations continue, schools and universities are advising users to remain alert for phishing attempts and suspicious communications.
For ongoing updates and technical details related to the breach itself, see our full coverage of the Instructure Canvas incident.