ShinyHunters has claimed a data breach at Carnival Corporation, the world’s largest cruise operator, alleging the theft of over 8.7 million records containing personally identifiable information alongside terabytes of internal corporate data. The claim surfaced April 18, 2026. Carnival has confirmed a phishing incident but has not verified the scope of the alleged exfiltration.
What Carnival Has Confirmed
Carnival acknowledged suspicious activity in a public statement, attributing the intrusion to a phishing attack targeting a single user account. “We acted quickly to block unauthorized activity following a phishing incident involving a single user account,” the company said. “We’re working with top global security experts to better understand the scope of the activity.” Carnival has not confirmed whether customer data was compromised, how many individuals may be affected, or what categories of data were accessed. The investigation is described as ongoing.
ShinyHunters claims the exfiltration covered over 8.7 million records of PII and additional terabytes of internal corporate data. The specific data types, whether passenger records, employee files, passport numbers, or operational documents, have not been independently verified.
A Familiar Attack Vector for a Repeat Target
The phishing vector Carnival described is the same entry point the company has faced repeatedly over the past seven years. Between 2019 and 2021, Carnival suffered 4 separate security incidents: 2 ransomware attacks and 2 phishing intrusions that collectively exposed passport numbers, Social Security numbers, dates of birth, health information, and payment card data belonging to customers, employees, and crew across Carnival Cruise Line, Holland America Line, Princess Cruises, and Costa Cruises.
The regulatory fallout was significant. A 46-state attorney general coalition reached a $1.25 million settlement with Carnival in 2022 over its 2019 breach, which exposed data on 180,000 individuals. The New York Department of Financial Services separately fined the company $5 million. As conditions of those settlements, Carnival agreed to implement mandatory phishing training for employees, enforce multi-factor authentication for remote email access, and adopt enhanced network monitoring. The 2026 incident originated from a phishing attack on a single account, the same vector Carnival was specifically required to harden against as part of those agreements.
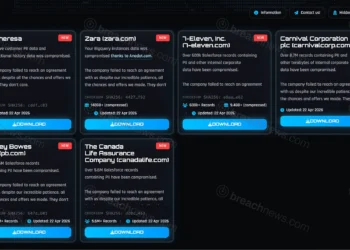
ShinyHunters’ Broader April Campaign
The Carnival claim is part of a wider ShinyHunters activity wave in mid-April that named at least 9 major organizations across multiple industries. Other victims listed in the same period include Zara parent company Inditex, which confirmed unauthorized database access and linked the incident to a compromise at a third-party technology provider, as well as 7-Eleven, Medtronic, Pitney Bowes, and Canada Life Assurance Company. Several of those listings have been tied to the group’s ongoing Salesforce misconfiguration exploitation campaign, covered previously in our reporting on Hallmark Cards and the broader Amtrak and McGraw-Hill wave. The Carnival listing does not appear connected to either the Salesforce campaign or the earlier Anodot-Snowflake wave that affected Rockstar Games and others. Carnival’s own statement points to a direct phishing compromise rather than a third-party platform pivot.
ShinyHunters is one of the most prolific financially motivated threat actors currently active, with confirmed prior breaches including Ticketmaster, Santander Bank, the European Commission, and most recently Vercel. The group consistently operates on a data exfiltration and extortion model, gaining initial access through phishing, vishing, or third-party platform compromise before issuing pay-or-leak demands.
If you have received a data breach notification, visit our guide on how to respond.