Educational technology company Instructure has confirmed it reached an agreement with the threat actors behind the recent Canvas breach after attackers threatened to leak allegedly stolen data tied to thousands of schools and universities.
Instructure, the parent company of the Canvas learning management platform, disclosed that it negotiated with the attackers following concerns over the potential publication of customer data reportedly exfiltrated during the intrusion.
The company said the agreement applies to all impacted customers and claims the stolen data was returned alongside what it described as digital confirmation of destruction. Instructure also stated it was informed that affected schools and universities would not face separate extortion demands tied to the incident, a claim later echoed in a statement published by the ShinyHunters operation.
The breach has been linked to the ShinyHunters extortion group, which previously claimed to have stolen approximately 3.65 TB of data from Canvas environments impacting nearly 9,000 organizations.
The latest disclosure follows earlier BreachNews reporting after Instructure confirmed a data breach tied to alleged mass student data theft and a subsequent escalation that saw schools and universities across the United States report potential exposure linked to the incident.
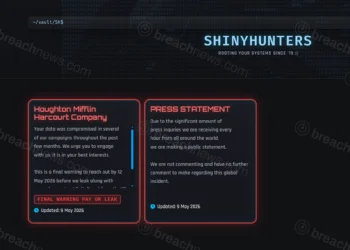
Shortly after Instructure disclosed the agreement, the ShinyHunters operation published a statement appearing to confirm the resolution. In the post, the group claimed it would not pursue further extortion against affected institutions and asserted that the allegedly stolen data was “nonexistent,” though those claims could not be independently verified.
The statement also instructed impacted organizations to stop attempting contact regarding payment negotiations, writing that “the matter has been resolved.”

Second wave of activity escalated pressure campaign
According to Instructure, attackers conducted a second wave of unauthorized activity on May 7 after the company initially believed the incident had been contained.
The additional activity reportedly included defacement of Canvas login portals across hundreds of institutions with extortion-related messages demanding negotiations before a May 12 deadline.
The incident previously expanded beyond Instructure itself after multiple universities, K-12 districts, and statewide education systems disclosed they were assessing potential impact tied to their Canvas environments.
Earlier reporting from BreachNews documented how the Canvas breach escalated as schools across the U.S. reported potential exposure of student information tied to the incident.
Instructure said the attackers exploited a vulnerability involving support tickets within its Free-for-Teacher environment to gain initial access. The company claims approximately 275 million records were exposed, including usernames, email addresses, course names, enrollment information, and messages.
The company stated that passwords, course submissions, and course content were not compromised during the incident.
As part of its response, Instructure said it revoked privileged credentials and access tokens, rotated internal keys, restricted token creation pathways, and implemented additional security controls. The company also temporarily disabled Free-for-Teacher accounts.
Education sector faces growing extortion pressure
The incident highlights the growing pressure ransomware and extortion groups are placing on educational technology providers and centralized learning platforms that service large numbers of institutions simultaneously.
Security researchers warned the exposed data could still be weaponized in targeted phishing campaigns against students, parents, faculty, and administrators by leveraging enrollment details and institutional context.
The decision to negotiate with attackers remains controversial across the cybersecurity industry, though organizations increasingly face pressure to prevent publication of sensitive downstream customer information during large-scale extortion incidents.
Additional technical details regarding the exploited vulnerability have not yet been publicly disclosed.
Further reporting and technical details were first published by The Hacker News.