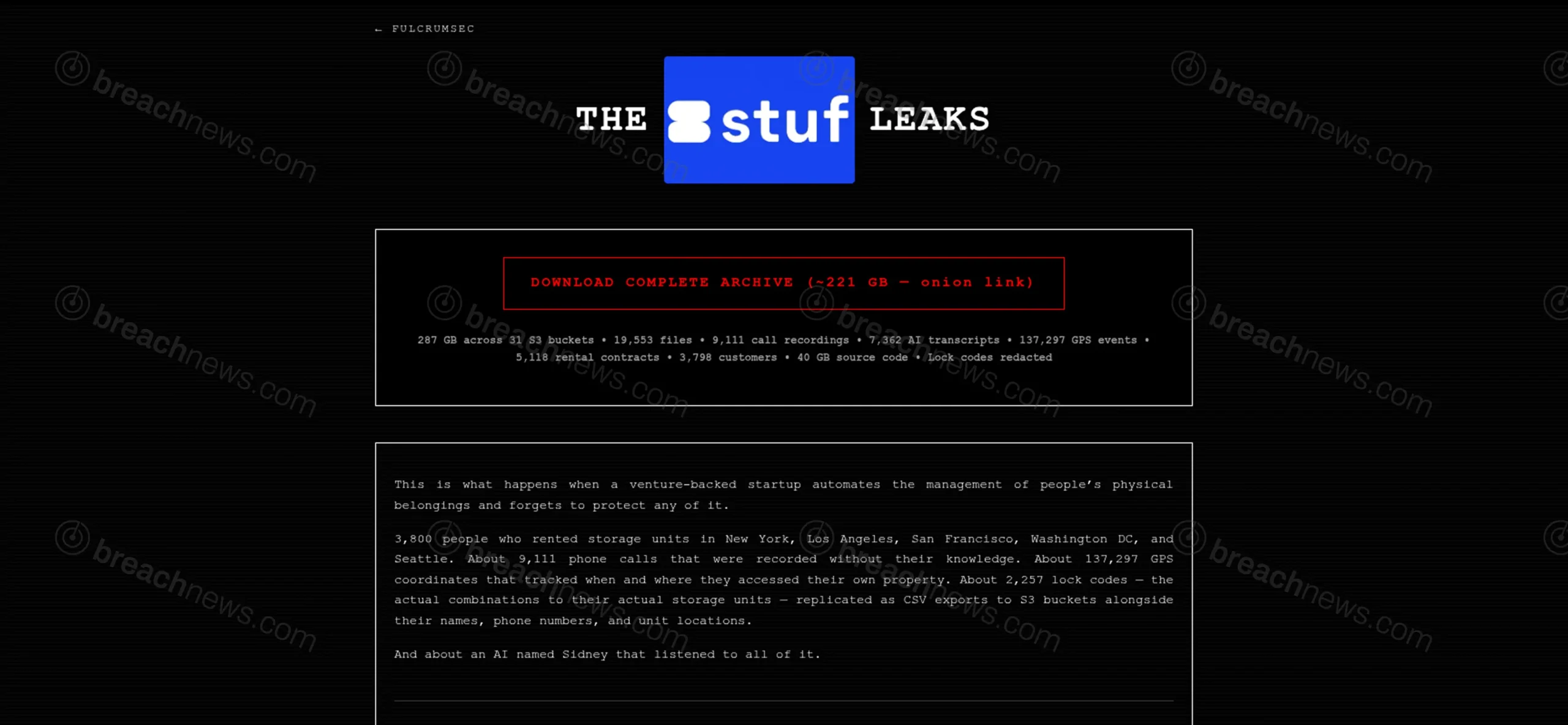
A threat actor operating under the name FulcrumSec has claimed responsibility for a large-scale data breach involving Stuf Storage, a U.S.-based self-storage provider, alleging the exfiltration of 287GB of sensitive data from the company’s cloud infrastructure.
The claim includes exposure of customer data, internal systems, and operational records, with particular emphasis on physical access information tied to storage facilities. The company had not issued any public statement at time of publication.
Alleged dataset includes physical access and surveillance-related data
According to the threat actor, the compromised data was obtained from multiple AWS S3 storage buckets and includes a wide range of sensitive information related to both customers and internal operations.
The allegedly exposed data includes rental contracts, customer contact details, call recordings, AI-generated call transcripts, SMS communications, and system logs tied to physical access events.
Of particular concern are claims that the dataset contains unit-level lock codes, facility entry codes, and detailed logs of physical access activity, including timestamped events and associated location data. The threat actor claims certain sensitive access codes were withheld from public release, though this has not been independently verified.
AI-driven call handling system raises data exposure concerns
The breach claim also highlights a large volume of recorded customer calls and AI-generated transcripts, reportedly captured through an automated voice system used by the company.
The transcripts were allegedly generated by an AI-driven voice platform designed to handle customer interactions, analyze sentiment, and store conversation data for operational insights. This suggests the system may have been systematically capturing and retaining detailed behavioral and conversational data at scale.
These records reportedly include customer conversations, support interactions, and automated analysis outputs. If accurate, the exposure of such data could present significant privacy implications, particularly if recordings were collected or retained without adequate safeguards.
Source code and internal systems allegedly exposed
FulcrumSec claims the breach extends beyond customer data to include approximately 40GB of internal source code across multiple repositories, along with access to backend systems and application components.
The dataset also reportedly includes database exports, API credentials, and internal platform components, which could enable deeper access to backend systems if verified.
The inclusion of application code and credentials could increase the risk of follow-on attacks, including exploitation of internal services or impersonation of platform functionality.
Cloud storage exposure cited as entry point
The threat actor attributes the breach to misconfigured or exposed cloud storage infrastructure, specifically AWS S3 environments used to store production data exports and system backups.
This aligns with a broader pattern of breaches involving improperly secured cloud storage, where sensitive data is accessible due to misconfiguration or insufficient access controls.
FulcrumSec claims the data has been made available for download, though BreachNews has not independently verified the dataset.
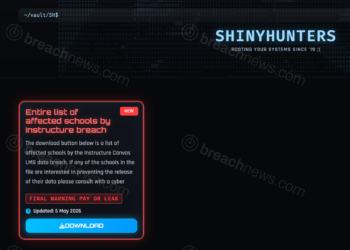
FulcrumSec continues pattern of large-scale data exposure claims
The group behind the claim has been linked to multiple recent incidents involving large-scale data exposure and system compromise, including the MyComplianceOffice dataset release and the Hatica engineering platform breach.
While the credibility of individual claims varies, the group has previously followed through on data releases after failed negotiations, increasing the potential risk associated with this incident.
The breach remains unverified, and the full scope and impact on Stuf Storage customers and operations are currently unknown.