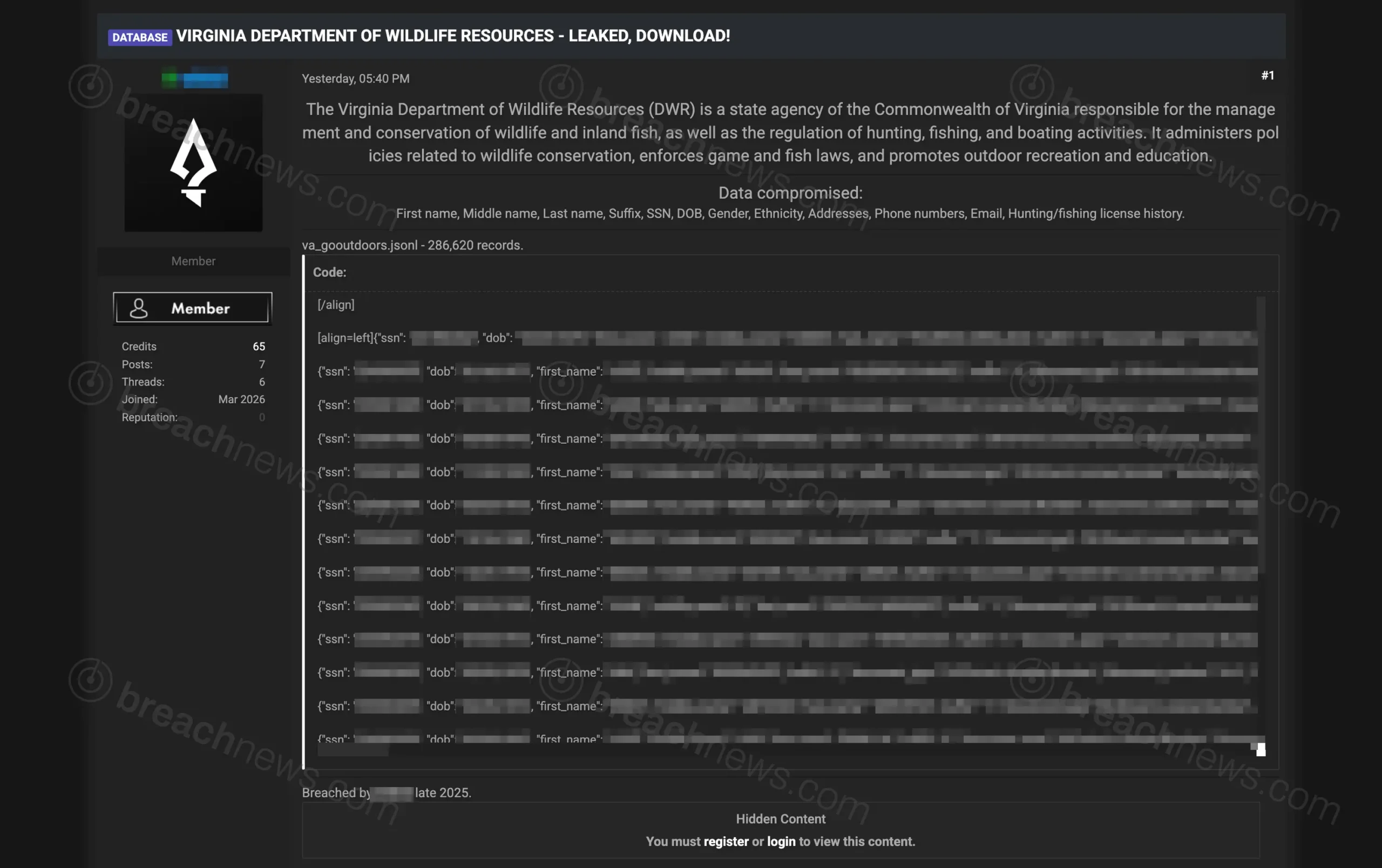
A threat actor has leaked a dataset allegedly tied to the Virginia Department of Wildlife Resources (DWR), claiming the records contain sensitive information belonging to more than 286,000 individuals.
The dataset was posted publicly on an open web forum and allegedly includes full names, Social Security numbers, dates of birth, driver’s license information, phone numbers, email addresses, physical addresses, and hunting and fishing license history.
The forum post claims the Virginia DWR data was originally breached in late 2025, though the records only recently began circulating publicly.
Sample records reviewed by BreachNews appeared to contain structured data consistent with wildlife licensing systems, including permit transaction histories and customer profile information tied to recreational licenses.
However, portions of the dataset also showed irregularities that raise questions about whether parts of the leaked data may have been duplicated, reformatted, or aggregated prior to release.
Sample data contains repeated transaction histories
Multiple records posted alongside the leak contained nearly identical transaction histories and repeated transaction identifiers despite belonging to different individuals.
Several entries reviewed by BreachNews included the same purchase dates, transaction numbers, and fishing license records replicated across unrelated profiles. That type of duplication is unusual in legitimate production exports and may indicate templated records, flawed parsing, or partially duplicated source data.
At the same time, some records referenced transactions dated as recently as 2025, suggesting at least portions of the information may still be relatively current if authentic.
The leaked data was distributed in JSONL format and appears structurally similar to exports generated by modern customer or licensing management platforms.
Possible third-party platform involvement remains unclear
It remains unclear whether the data originated directly from Virginia DWR infrastructure or from a third-party vendor connected to hunting and fishing license management systems.
Many state wildlife agencies rely on external providers to process online license purchases, customer records, permit management, and payment workflows. If authentic, the dataset could potentially originate from one of those integrated systems rather than a direct compromise of state government infrastructure.
The alleged leak surfaced alongside another wildlife-related dataset involving Texas Parks and Wildlife that appeared online around the same timeframe, potentially pointing to a shared source or related licensing ecosystem.
At time of publication, the Virginia Department of Wildlife Resources had not issued any public statement regarding the alleged leak.
Exposure could create identity theft and phishing risks
Although the actor does not currently appear tied to a major extortion or ransomware operation, the dataset allegedly contains enough personally identifiable information to support identity theft, phishing attacks, or targeted fraud campaigns if the records are authentic.
The incident also highlights growing concerns around centralized licensing and recreational management systems that store large volumes of sensitive citizen data across multiple states and agencies.
BreachNews has not independently verified the full dataset or confirmed whether the records originated from a direct compromise of Virginia DWR systems.
Individuals potentially affected should remain cautious of unsolicited communications, suspicious verification requests, or phishing emails referencing hunting, fishing, or state licensing accounts.