Threat actor FulcrumSec has claimed responsibility for an alleged breach involving Arup Group, the multinational engineering and infrastructure consulting firm behind major transportation, energy, urban development, and public infrastructure projects worldwide.
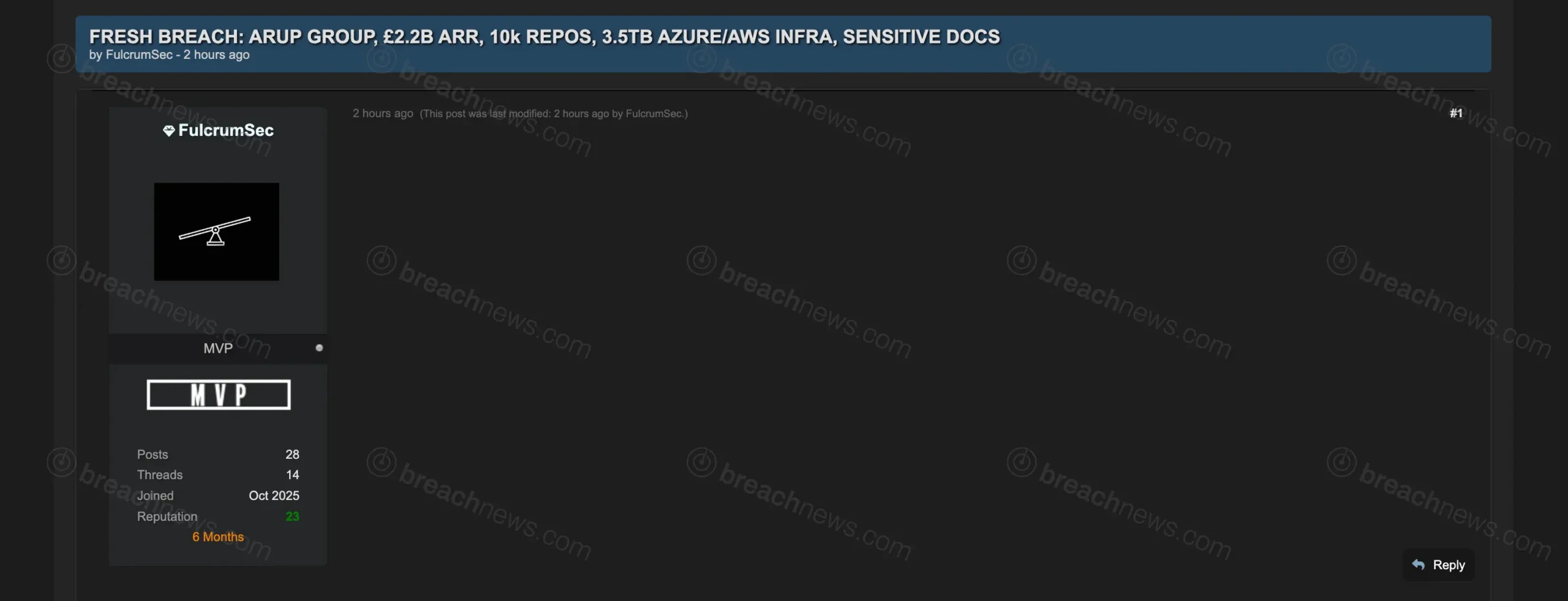
The claim appeared in a newly created forum thread titled:
FRESH BREACH: ARUP GROUP, £2.2B ARR, 10k REPOS, 3.5TB AZURE/AWS INFRA, SENSITIVE DOCS
At the time of publication, however, the thread body itself appeared blank, containing no publicly visible proof package, screenshots, file samples, or technical details supporting the claim.
Despite the lack of evidence, the post has drawn attention because of FulcrumSec’s prior activity targeting enterprise software firms, SaaS providers, cloud environments, and corporate platforms. The actor has previously claimed breaches involving organizations in the financial services, healthcare, technology, and engineering sectors.
According to the thread title, the actor allegedly obtained access to:
- 10,000 repositories
- 3.5TB of Azure and AWS infrastructure data
- Sensitive internal documents
- Corporate assets associated with Arup Group
No data samples or independent verification were available at publication time.
Cloud and repository access claims raise potential infrastructure concerns
If legitimate, the alleged compromise could represent a significant exposure for a company operating across critical infrastructure, transportation, architecture, engineering, and smart-city development sectors.
Engineering firms like Arup often maintain large repositories containing:
- Infrastructure schematics
- Architectural models
- Transportation and civil engineering documents
- Cloud-hosted project environments
- Government and contractor communications
- Internal software repositories and automation tooling
Access to large repository environments can also expose embedded credentials, API keys, infrastructure-as-code configurations, and cloud deployment pipelines if development environments are improperly segmented.
The claim specifically references both Azure and AWS infrastructure, potentially indicating access to hybrid cloud environments rather than a single compromised platform.
Blank forum thread leaves major questions unanswered
The unusual aspect of the claim is that the forum thread itself contained no visible body content beyond the title at the time it was observed.
That leaves several possibilities open, including:
- The actor reserved the thread before uploading evidence
- The post content was temporarily removed or hidden
- The thread was improperly published
- The actor intends to release proof material later
Without screenshots, archive listings, sample files, or leaked documents, there is currently no way to independently verify the scope or legitimacy of the alleged breach.
FulcrumSec has nevertheless developed a reputation for targeting enterprise-focused organizations rather than posting low-effort credential dumps or recycled consumer databases. Previous claims attributed to the actor have included allegations involving cloud platforms, operational systems, internal source code, and corporate document repositories.
Arup had not issued any public statement at time of publication.
The company, headquartered in the United Kingdom, operates globally across engineering, architecture, sustainability, transportation, energy, and infrastructure sectors. Arup has participated in major international projects involving airports, rail systems, stadiums, bridges, urban infrastructure, and public-sector developments.
BreachNews will continue monitoring the situation for additional evidence, public disclosures, or confirmation from the company.