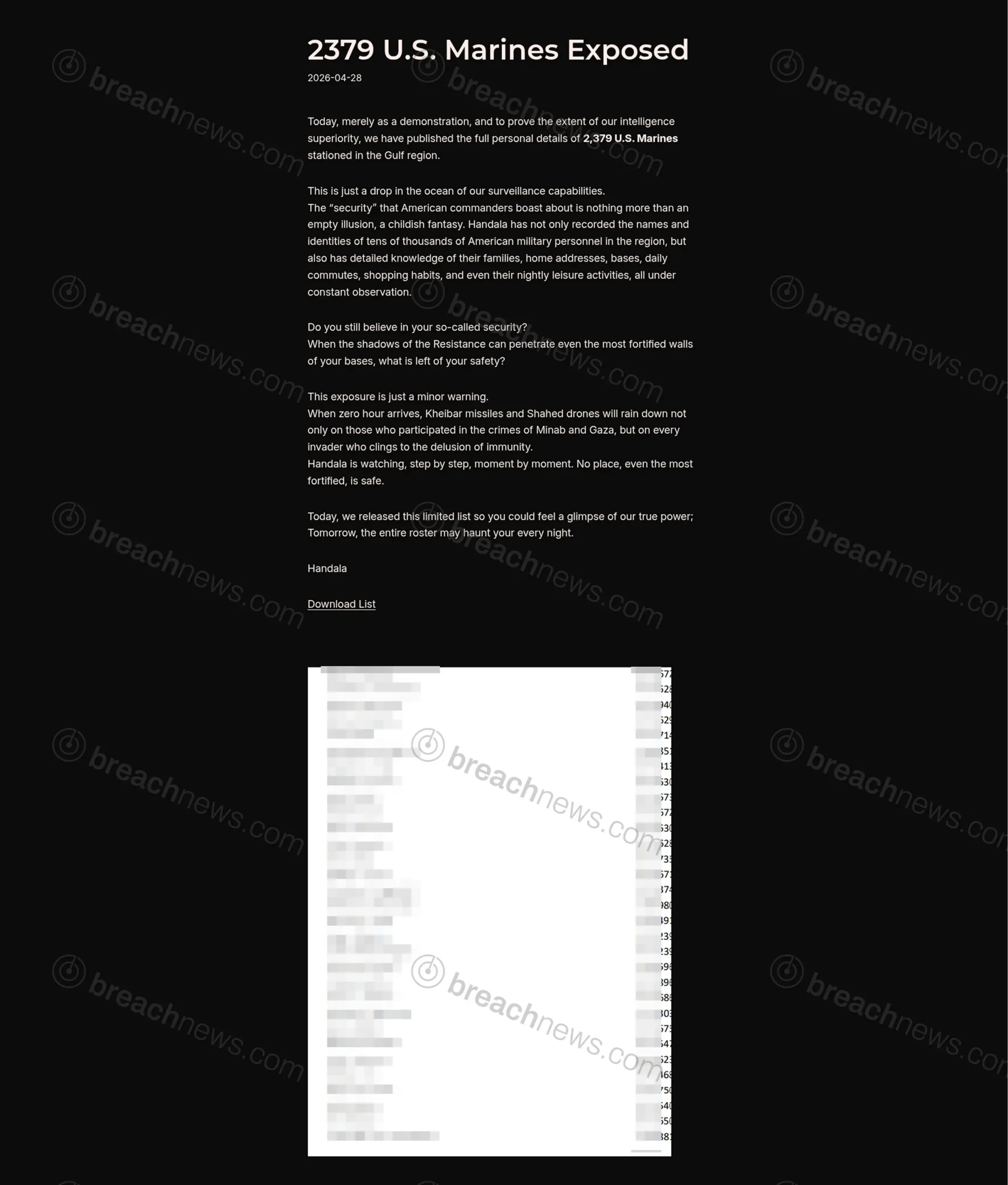
The pro-Iranian hacktivist group Handala Hack claims it has exposed the personal details of 2,379 U.S. Marines stationed in the Gulf region, publishing what it describes as a limited dataset to demonstrate broader intelligence capabilities.
The April 28, 2026 post frames the release as a warning rather than a financial extortion attempt, with the group asserting it holds significantly more data on U.S. military personnel and their families. The authenticity of the dataset and the source of the information have not been independently verified.
“Demonstration” release signals broader intelligence claims
Handala states the published dataset represents only a fraction of its access, claiming visibility into tens of thousands of U.S. personnel across the region. The group alleges it possesses detailed intelligence including identities, family connections, home addresses, base assignments, commuting routines, and daily activity patterns.
The messaging is explicitly psychological, aimed at undermining confidence in U.S. military security posture rather than initiating a traditional ransom negotiation.
Unclear source raises questions about data origin
It remains unclear whether the exposed data originates from a direct compromise of military or contractor systems, aggregation of previously leaked datasets, or open-source intelligence collection combined with enrichment techniques.
Similar claims in past operations have ranged from legitimate breaches to exaggerated or recycled datasets. Without independent validation, the scope and sensitivity of the exposed records cannot be confirmed.
Operational and personal security risks if verified
If the claims are accurate, the exposure could carry significant implications for both operational security and personal safety. Data of this nature could be leveraged for targeted phishing campaigns, identity-based intelligence gathering, or attempts to track and profile military personnel and their families.
The inclusion of behavioral and routine-based intelligence, if genuine, would represent a higher level of surveillance capability than typical data breach incidents.
Part of a broader pattern of escalation by Handala
This latest claim follows a series of increasingly aggressive operations attributed to Handala Hack, including both data exposure and destructive cyberattack campaigns. BreachNews has previously documented the group’s claims of long-term access to infrastructure and targeted attacks on government and defense-linked entities.
Recent activity includes claims of 18-month persistent access to Israeli cloud infrastructure and destructive attacks involving large-scale data wiping, signaling a shift beyond simple data leaks into hybrid cyber and psychological operations.
The group has also previously claimed breaches involving sensitive targets, including defense contractors and media organizations, though not all claims have been independently verified.
Blending cyber operations with geopolitical messaging
The tone of the April 28 release reflects a continued shift toward hybrid operations that combine cyber activity with overt geopolitical messaging and intimidation tactics. The statement includes direct references to military action and surveillance, positioning the data exposure as part of a broader campaign rather than an isolated incident.
This approach aligns with a growing trend among politically motivated threat actors who use data exposure not just for access or profit, but as a tool for influence, deterrence, and psychological pressure.
No official response at time of publication
No U.S. government agency or Department of Defense entity had issued any public statement at time of publication regarding the alleged exposure.
As with similar claims, the lack of independent verification leaves open the possibility that the dataset is incomplete, outdated, or compiled from previously available sources. However, even partial accuracy could carry real-world implications given the sensitivity of the individuals involved.