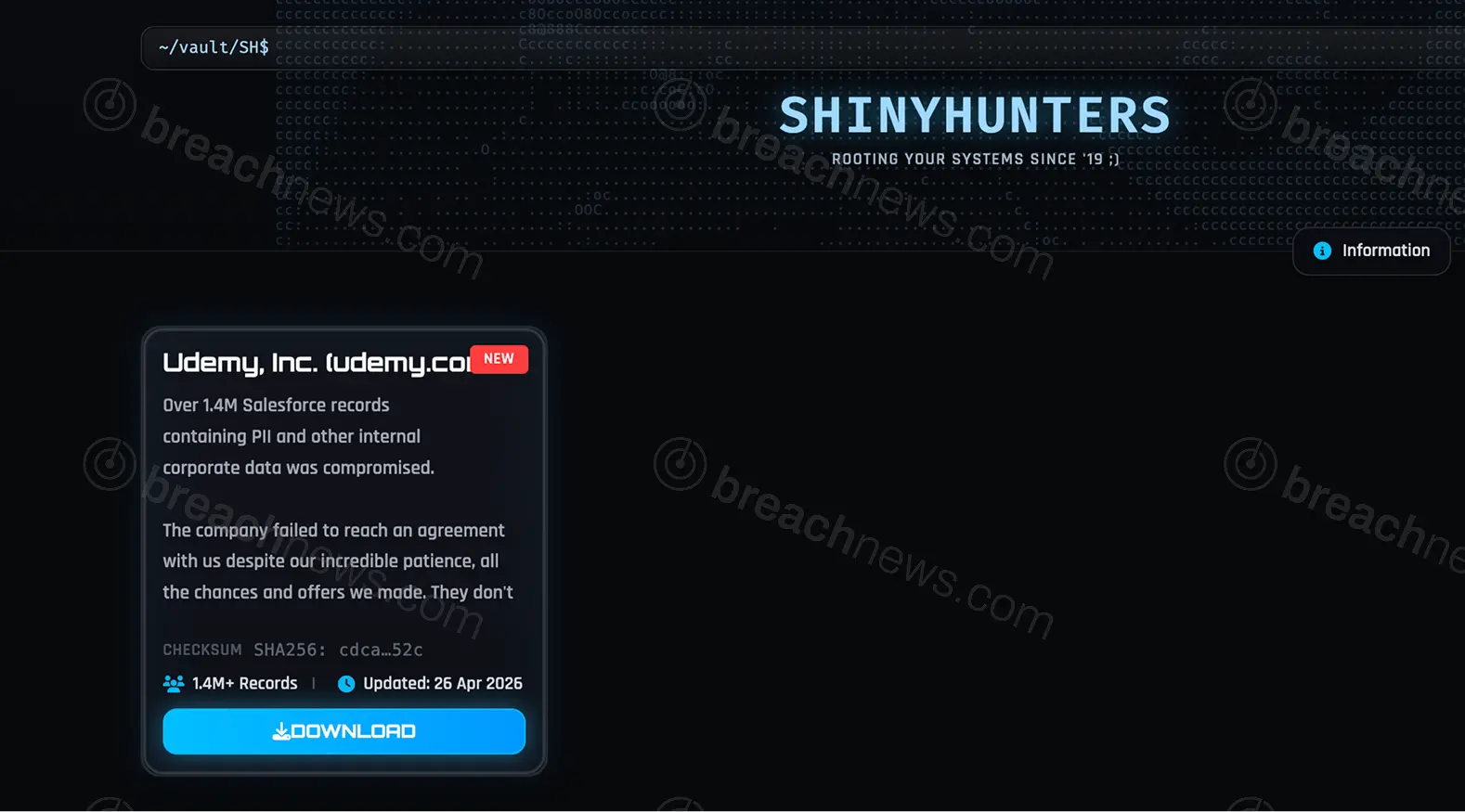
An alleged dataset tied to online learning platform Udemy has been published by ShinyHunters following what appears to be a failed extortion attempt. The data was reportedly listed on the group’s leak site on April 26, 2026, before being publicly released within days after negotiations failed.
Dataset publication follows reported pay-or-leak pressure
According to publicly shared details, the dataset contains approximately 1.4 million unique email addresses associated with Udemy customers and instructors. Additional information reportedly includes names, physical addresses, phone numbers, employer data, and instructor payout details such as PayPal, cheque, and bank transfer information.
The leak aligns with a broader pattern observed in ShinyHunters operations, where organizations are listed and given a window to negotiate before data is released. In this case, the publication suggests negotiations either failed or did not occur, resulting in the dataset being made publicly available.
Leaked dataset reportedly indexed by breach monitoring services
Following the reported publication, breach monitoring services have begun indexing portions of the dataset. Approximately 1.4 million unique email addresses have reportedly been identified, with associated records including names, addresses, phone numbers, employer information, and instructor payout details.
A significant portion of the exposed email addresses had previously appeared in other known breaches, suggesting overlap with existing datasets while still introducing new exposure risk for affected users.
Resurfacing data and secondary distribution adds complexity
The Udemy dataset has also begun appearing in secondary listings attributed to other threat actors, indicating redistribution beyond the original leak source. This pattern is increasingly common in large-scale breaches, where initial publications are quickly replicated, repackaged, and circulated across multiple platforms.
Similar behavior has been observed in recent ShinyHunters campaigns affecting multiple organizations. A coordinated wave of listings involving companies such as Zara, 7-Eleven, and Pitney Bowes followed a similar trajectory, with data exposure escalating after failed negotiations. Additional activity linked to Salesforce-related campaigns highlights the group’s continued focus on large-scale data extraction.
Instructor payout data raises additional risk concerns
Beyond standard customer information, the inclusion of instructor payout data introduces additional risk. Financial routing details, combined with identity information, can enable targeted fraud, phishing campaigns, and potential account takeover attempts.
Exposure of this type of data differs from typical credential leaks, as it may involve financial workflows and payment channels that are harder to secure once compromised.
It remains unclear whether the exposed records primarily relate to students, instructors, or a combination of both, though the inclusion of payout-related data suggests at least some instructor accounts are affected.
Part of broader ShinyHunters activity surge
The Udemy leak appears within a broader surge in ShinyHunters activity throughout April 2026, which has included multiple high-profile breach claims and data releases. BreachNews has previously reported on incidents involving Carnival Corporation, Marcus & Millichap, and ADT, all following similar extortion-driven patterns.
More details on the group’s operations and recent campaigns can be found in the ShinyHunters threat actor profile.
No confirmation from Udemy
Udemy had not issued any public statement at time of publication regarding the alleged breach or the reported data leak.
As with similar incidents, the claims surrounding the dataset remain based on threat actor activity and have not been independently verified. However, the reported public availability of the data represents a significant escalation beyond initial breach claims.