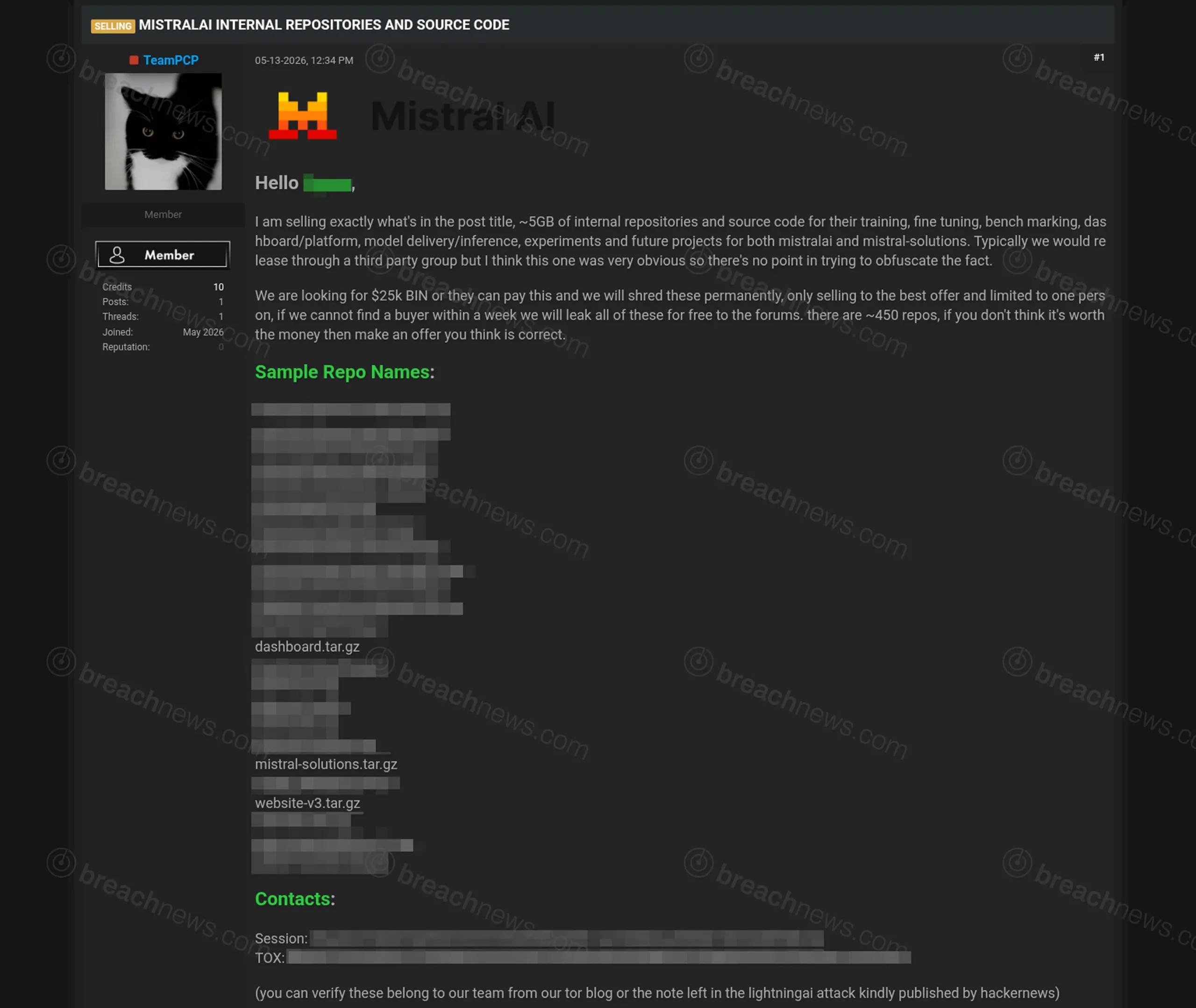
Actors identifying themselves as TeamPCP are claiming to possess internal repositories and source code allegedly stolen from French AI company Mistral AI, marking the latest development in what appears to be an expanding campaign targeting artificial intelligence and developer infrastructure platforms.
The post, published on May 13 and still publicly accessible as of May 15, advertises approximately 5 GB of alleged internal Mistral AI data containing what the actors describe as source code, training infrastructure, fine-tuning projects, inference systems, benchmarking tools, dashboards, and unreleased internal initiatives.
According to the claims, the archive allegedly contains roughly 450 repositories tied to both mistralai and mistral-solutions environments.
The actors also claimed they would either sell the data privately or permanently delete it if payment demands were met. The post stated that if no buyer emerged within one week, the repositories would allegedly be leaked publicly.
Claimed repository names point to AI infrastructure and enterprise tooling
Sample repository names published in the post appear related to model inference, fine-tuning, benchmarking, enterprise AI tooling, cloud infrastructure, and customer-facing AI systems.
Several repository names referenced internal inference environments, finance-related tooling, dashboard infrastructure, AI agent projects, and benchmarking systems potentially tied to model evaluation and deployment workflows.
BreachNews is intentionally withholding the majority of repository names because some appear to reference potentially sensitive internal projects, enterprise integrations, or customer-related tooling.
The claims have not been independently verified, and Mistral AI had not issued any public statement at time of publication.
Post references earlier Lightning AI incident
The alleged TeamPCP operators directly referenced the recent Lightning AI repository leak tied to the PyTorch Lightning supply-chain incident as part of the sales post, appearing to frame the previous intrusion as proof of authenticity for the newly claimed access.
That reference is notable because security researchers have increasingly linked TeamPCP to a growing number of software supply-chain and AI-focused intrusion campaigns involving developer tooling, CI/CD environments, cloud infrastructure, and source code repositories.
Earlier reporting from BreachNews also covered how the broader TeamPCP supply-chain activity targeted developer secrets and enterprise infrastructure through compromised software distribution mechanisms.
AI companies becoming increasingly attractive targets
The alleged Mistral AI exposure highlights growing attacker interest in artificial intelligence companies and the ecosystems surrounding model development, fine-tuning, cloud inference, and enterprise AI deployment.
Unlike traditional database breaches, source code and repository compromises can expose internal architecture decisions, deployment methods, security tooling, unreleased features, and infrastructure credentials capable of enabling deeper downstream compromise.
AI development environments may also contain access to proprietary datasets, model pipelines, benchmarking systems, cloud orchestration frameworks, and customer integrations that attackers could potentially weaponize for further intrusion activity or extortion.
The timing of the claims also aligns with broader concerns surrounding attacks on open-source ecosystems and trusted software infrastructure following the recent Mini Shai-Hulud software supply-chain campaign, which demonstrated how attackers can abuse trusted publishing systems and CI/CD workflows to distribute malicious code at scale.
At this stage, it remains unclear whether the alleged Mistral AI data originated from direct compromise of internal infrastructure, third-party systems, developer credentials, or previously compromised environments.