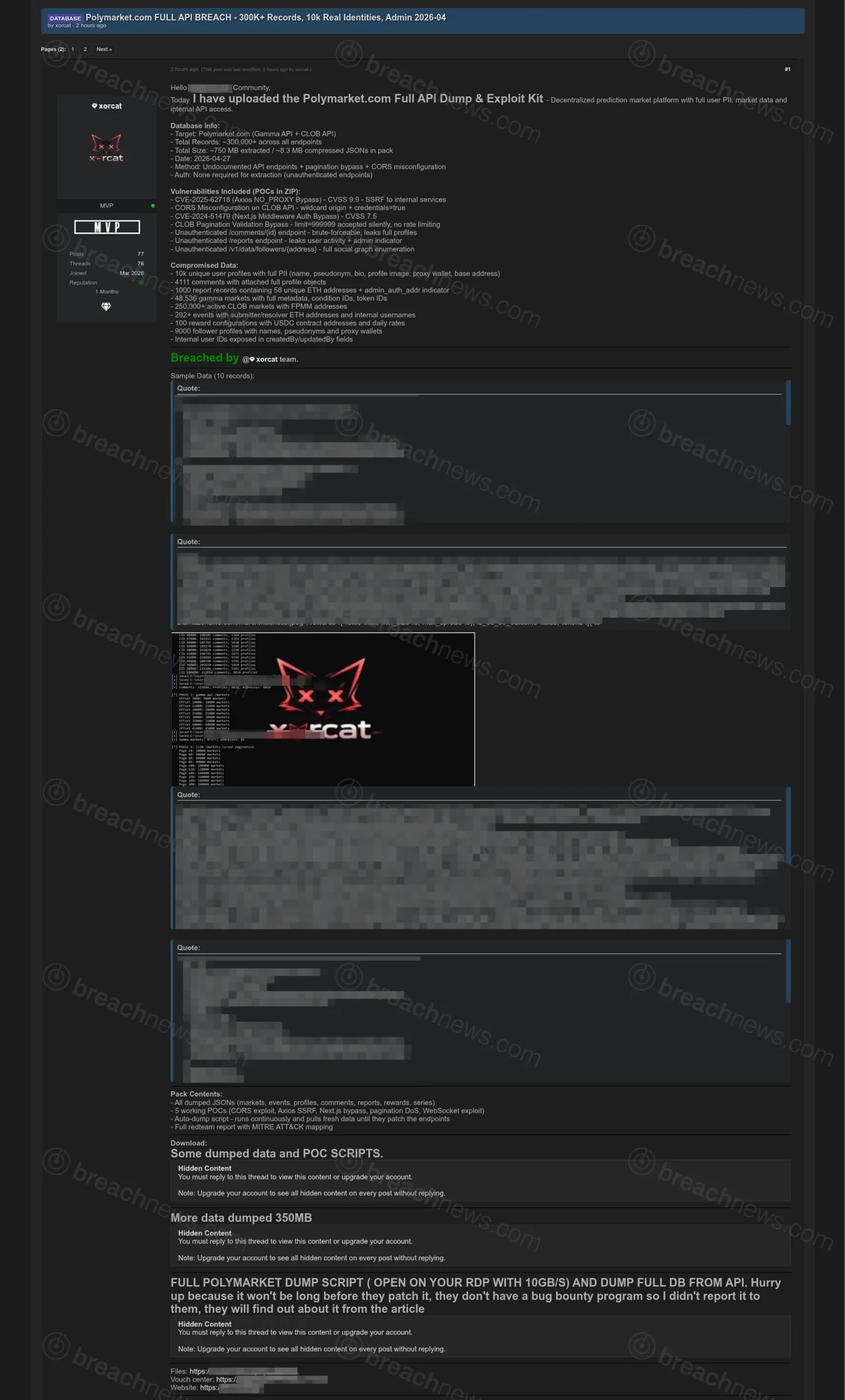
A threat actor known as xorcat is claiming to have extracted more than 300,000 records from Polymarket, a decentralized prediction market platform, by exploiting a series of alleged API misconfigurations and unauthenticated endpoints. The dataset, described as a “full API dump,” was posted April 27, 2026, alongside proof-of-concept scripts and exploitation details.
Alleged API weaknesses enabled large-scale data extraction
According to the listing, the data was obtained through a combination of exposed API endpoints, weak access controls, and misconfigured cross-origin resource sharing settings. The actor claims that no authentication was required to query certain endpoints, allowing automated extraction of user profiles, market data, and platform activity at scale.
Additional techniques reportedly included pagination manipulation to bypass limits and enumeration of user-related endpoints, enabling bulk collection of records without triggering rate limiting or access restrictions.
Claims include user profiles, social graph, and market data
The dataset is described as containing approximately 300,000 records across multiple API endpoints, including around 10,000 user profiles. The exposed information reportedly includes usernames, pseudonyms, wallet addresses, profile metadata, and follower relationships, along with extensive market data tied to Polymarket’s prediction platform.
While the actor characterizes the dataset as containing “full PII,” the available samples suggest the data is largely limited to account-level and blockchain-linked identifiers rather than traditional sensitive identifiers such as Social Security numbers or financial credentials.
Exploit chain references multiple vulnerabilities
The post references several alleged vulnerabilities, including CORS misconfiguration, API authorization bypasses, and issues tied to known libraries and frameworks. These include claims of an Axios proxy bypass and a Next.js middleware authentication flaw, though these have not been independently verified in the context of Polymarket’s environment.
The inclusion of proof-of-concept scripts and automated dumping tools suggests the actor may have been able to continuously extract data until the endpoints are secured, raising concerns about ongoing exposure if the issues remain unpatched.
Misconfiguration rather than intrusion appears likely scenario
Based on the technical details provided, the incident appears more consistent with large-scale data exposure due to API design and configuration issues rather than a traditional network intrusion or database breach.
Polymarket has previously faced security incidents in 2025 and early 2026 involving account compromise and trading vulnerabilities, but the current claims point to a separate issue tied to API exposure and access control weaknesses.
Such exposures are increasingly common in modern web applications, where API-first architectures can unintentionally expose sensitive or internal data when authentication and access controls are not properly enforced.
Part of broader trend in API-driven data exposure
API misconfigurations and unauthenticated endpoints have become a frequent source of data exposure incidents, particularly in platforms handling user-generated content and real-time data. Similar patterns have been observed in other recent incidents involving improperly secured cloud and application interfaces.
BreachNews has previously reported on cases involving cloud storage exposure and misconfigured systems, including AWS misconfiguration-driven data leaks, highlighting how non-intrusive access paths can still result in large-scale data exposure.
No confirmation from Polymarket
Polymarket had not issued any public statement at time of publication regarding the alleged exposure or the claims made by the threat actor.
As with similar incidents, the claims remain unverified and are based on threat actor-provided information. The extent of the exposure, the validity of the vulnerabilities, and whether the data was publicly accessible or improperly secured are still unclear.