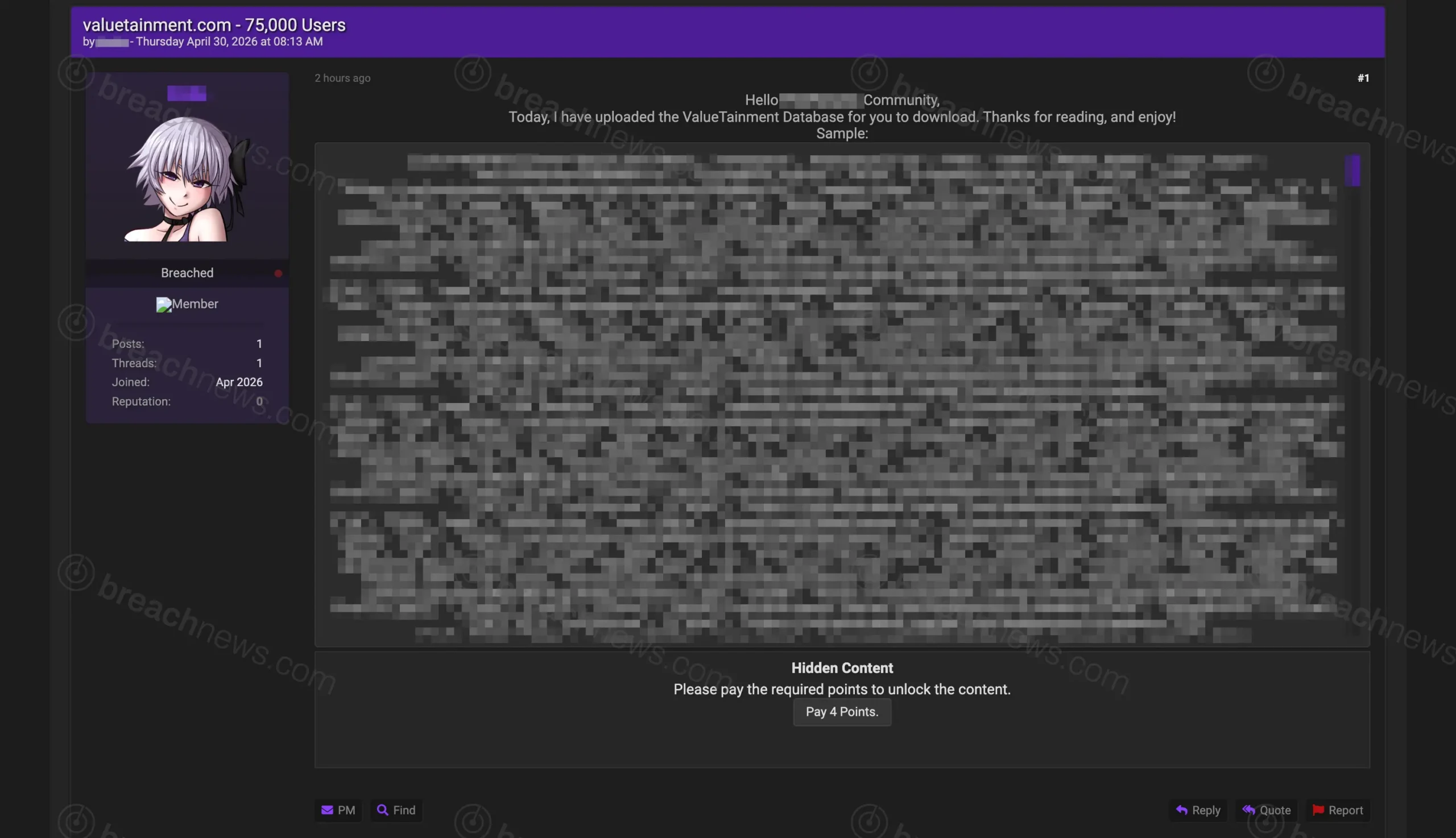
A threat actor has claimed to have leaked a database allegedly belonging to Valuetainment, a media platform known for its business and entrepreneurship content, including the PBD Podcast. The claim involves approximately 75,000 user records and was posted April 30, 2026 on a cybercrime forum.
The actor, who appears to be newly active with no prior established track record, provided a small sample of the dataset to support the claim. The authenticity and full scope of the data have not been independently verified.
Recent breach claims involving media and platform-based user data have followed similar patterns, including the alleged Udemy dataset leak, where initial claims evolved as more evidence surfaced.
Sample data suggests member profile exposure
The sample provided appears to consist of structured JSON records tied to user profiles, likely from a membership or community system. Based on analysis, the data may include names, email addresses used as login identifiers, user profile links, and internal metadata associated with account profiles.
The structure of the data strongly suggests it originates from a WordPress-based BuddyPress membership system, with records pulled from REST API endpoints exposing user profile data.
Some records appear to reference membership categories such as VIP or podcast-related tiers, suggesting the dataset may be tied to Valuetainment’s community or subscription features.
No passwords, payment data, or sensitive financial information were visible in the sample reviewed. However, email exposure alone can present risk for phishing and credential-stuffing attacks.
Limited detail around scope and origin
The forum post provides minimal technical detail beyond the claimed record count and a small sample of data. It does not specify how the dataset was obtained, when the data was accessed, or whether the information reflects a current or historical snapshot.
There are no clear indicators yet whether this represents a direct compromise of Valuetainment systems, exposure through a third-party service, or data collected via publicly accessible endpoints or automated scraping.
Without additional context or independent verification, the scope and origin of the dataset remain unclear.
Possible API or community platform source
The structure of the data suggests it may originate from a web API tied to a WordPress BuddyPress community system. References to profile endpoints and structured user objects point to REST API exposure rather than a traditional backend database compromise.
The presence of BuddyPress API endpoints in the sample suggests the data may have been obtained through exposed or misconfigured application interfaces, rather than a direct compromise of backend systems.
If confirmed, this could indicate either misconfigured access controls or unintended public exposure rather than a traditional intrusion.
No public statement from Valuetainment
Valuetainment had not issued any public statement at time of publication regarding the alleged breach or the dataset being circulated.
Given the limited evidence and the lack of a known actor track record, the claim should be treated with caution. Further verification is required to determine whether the data is authentic, how it was obtained, and whether users are at risk.